Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Upping the Auditing Game for Correlation Searches Within Enterprise Security - Part 1: The Basics
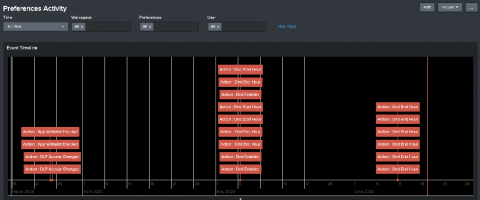
One question I get asked frequently is “how can I get deeper insight and audit correlation searches running inside my environment?” The first step in understanding our correlation searches, is creating a baseline of what is expected and identify what is currently enabled and running today. Content Management inside Splunk Enterprise Security is a quick way to filter on what is enabled (and it’s built into the UI and works out of the box).
What Is a Cybersecurity Audit and Why Does it Matter?
Splunking Slack Audit Data
The Slack Audit Logs API is for monitoring the audit events happening in a Slack Enterprise Grid organization to ensure continued compliance, to safeguard against any inappropriate system access, and to allow the user to audit suspicious behavior within the enterprise. This essentially means it is an API to know who did what and when in the Slack Enterprise Grid account. We are excited to announce the Slack Add-on for Splunk, that targets this API as a brand new data source for Splunk.
Netwrix Auditor for Windows File Servers - Overview
When's the Right Time for an Open Source Audit?
How much do you really know about your open source usage? Can you identify what open source components you’re using? How about which licenses are in play and whether you’re compliant? Do you have a good sense of how many open source security vulnerabilities are in your code base and how to remediate them? Chances are, if you’re like most organizations, you can’t answer all of these questions.
A Checklist for Preparing for Your Organization's Next PCI Audit
Organizations cannot afford to neglect their PCI compliance obligations. According to its website, PCI could punish offending organizations with a monetary penalty ranging in value from $5,000 to $100,000 per month. These fines could spell the end for a small business. Acknowledging those consequences, organizations need to make sure they’re PCI compliant. More than that, they must ensure they’re prepared for when auditors come knocking on their door.