Understanding Splunk Phantom's Join Logic
If you’re an active Splunk Phantom user, it’s safe to assume you know what a playbook is. If not, here’s a quick summary: Phantom playbooks allow analysts to automate everyday security tasks, without the need for human interaction. Manual security tasks that used to take 30 minutes can now be executed automatically in seconds using a playbook. The result? Increased productivity and efficiency, time saved, and headaches avoided.
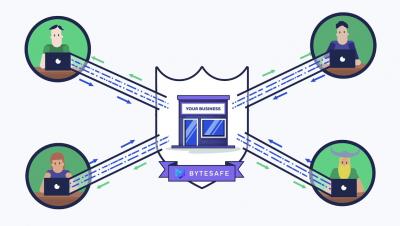
How to prepare your business for secure cloud migration
The cloud holds a lot of potential for organisations. Moving your IT environment to a secure cloud provides flexibility and agility. It allows your team to be more productive and focus on delivering value for your business. Protecting your assets, particularly your data, will help you remain secure while your organisation scales using the cloud. As you prepare for cloud migration, it’s crucial that you have the buy-in from your whole organisation.
Security Updates for June 1
Our Crowdsource ethical hacker community has been busy sending us security updates, including 0-day research. For Asset Monitoring, we now push out tests more frequently at record speed within 25 minutes from hacker to scanner. Due to confidentially agreements, we cannot publicize all security update releases here but they are immediately added to our scanner and available to all users.
How to Proactively Plan Threat Hunting Queries
As your security capabilities improve with centralized log management, you can create proactive threat hunting queries. Setting baselines, determining abnormal behavior, and choosing an attack framework helps you mitigate risk and respond to incidents. To reduce key metrics like the mean time to investigate (MTTI) and mean time to respond (MTTR), security operations teams need to understand and create proactive queries based on their environments.
Going Beyond Exclude Patterns: Safe Repositories With Priority Resolution
You probably remember the Namespace Shadowing a.k.a. “Dependency Confusion” attack that was in the news a couple of weeks ago. I blogged back then about the Exclude Patterns feature of JFrog Artifactory which we’ve had forever and was always intended to protect you against those kinds of attacks.
Outpost24 - Full stack vulnerability management and security assessment
How to Apply the Risk Management Framework (RMF)
The Risk Management Framework (RMF) is most commonly associated with the NIST SP 800-37 guide for “Applying the Risk Management Framework to Federal Information Systems: A Security Life Cycle Approach,” which has been available for FISMA compliance since 2004. It was updated in December 2018 to revision 2. This was the result of a Joint Task Force Transformation Initiative Interagency Working Group; it’s something that every agency of the U.S.
Understanding the Cloud Security Challenges for SMBs
The events of 2020 didn’t prevent small- to mid-sized businesses (SMBs) from adopting the cloud. Impact Networking reported that SMBs’ overall cloud spending grew 6.3% between 2019 and 2020. Such growth is projected to lead more than a third (35%) of SMBs to annually spend between $600,000 and $1.2 million on public cloud services by the end of 2021, noted Statista.