You Can't Secure AI Agents You Haven't Found
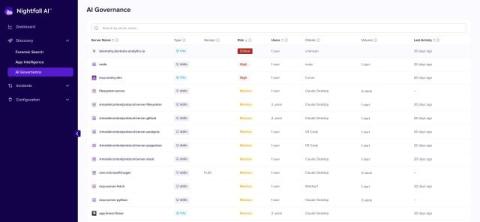
Most organizations have a reasonable handle on their sanctioned SaaS apps. Model Context Protocol - hit 10,000 public servers within a year of launch, with 97 million monthly SDK downloads. None of those numbers capture the servers your developers configured locally. Those don't appear in any registry. They were added at the IDE level, one developer at a time, with no approval step and nothing that touches a central system. That's the inventory problem. It comes before any question of enforcement.