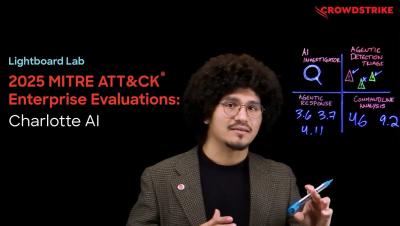
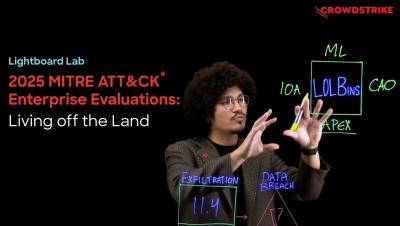
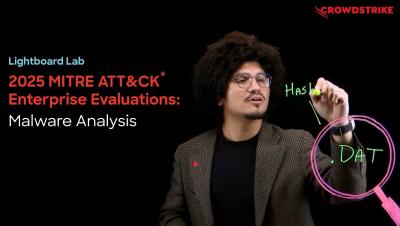
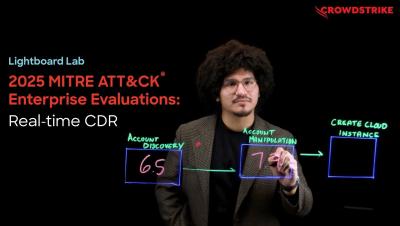
CrowdStrike Leads the Way in the 2025 MITRE ATT&CK Enterprise Evaluations
The results of the 2025 MITRE ATT&CK Enterprise Evaluations are in and CrowdStrike excelled, achieving 100% detection, 100% protection, and zero false positives. The MITRE ATT&CK evaluation is an independent assessment that tests how cybersecurity products detect and stop real-world adversary behavior. The 2025 round was the most challenging cross-domain evaluation to date, a true platform test. For the first time, MITRE tested defenses across endpoint, identity, and cloud.