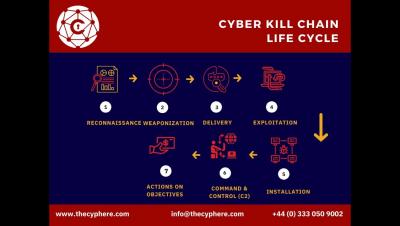
Cyber Kill Chain: What It Is, How It Works
What is the cyber kill chain? What is an example of the Cyber Kill Chain? What are the 7 steps of the cyber kill chain? Is the Cyber Kill Chain outdated? Cyber Kill Chain vs Mitre Att&ck Cyphere is a UK-based cyber security services provider helping organisations to secure their most prized assets. We provide technical risk assessment (pen testing/ethical hacking) and managed security services. This advice is a true third party opinion, free from any vendor inclinations or reselling objectives.