Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Identity fatigue - the security challenge that threatens identity processes and systems
There’s a new cybersecurity challenge threatening the identity processes and systems of organizations worldwide: identity fatigue.
SecurityScorecard's Partnership with the TSA
As part of our continued commitment to making the world a safer place, SecurityScorecard recently partnered with the Transportation Security Administration (TSA). This partnership will enable the agency to more accurately monitor and assess the cyber health of the nation’s pipeline, rail, and aviation transportation systems.
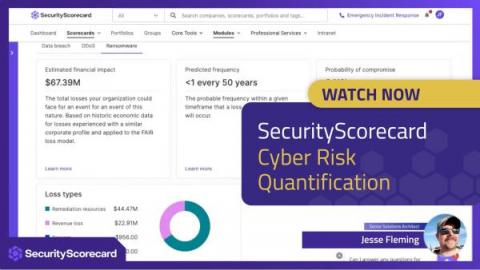
Translate Cyber Risk into Dollars With SecurityScorecard
Cyber risk is not just a security issue, it’s also a business issue. When security leaders and their businesses don’t see eye to eye, resources get misallocated, expectations aren’t met, and businesses are left unprepared to face threats. SecurityScorecard launched its Cyber Risk Quantification product in April 2022, allowing customers to quantify the financial impact of cyber risk and help facilitate collaboration and communication among business stakeholders.
Q1 2023 Privacy: In for Another Wild Year
2023 started much the same as the year before, with state legislatures producing an impressive list of privacy-related bills in the U.S. Twenty-three states introduced comprehensive privacy legislation, with many more targeted privacy bills being considered as well. Iowa's governor signed the sixth comprehensive privacy law to close out the quarter.
How to comply with PCI DSS 4.0 while juggling day-to-day tasks
In our webinar, Insights for Navigating PCI DSS 4.0 Milestones, we discuss some of the challenges organizations face as they try to comprehend the new requirements of PCI DSS 4.0.
How do Cloud Access Security Brokers (CASBs) Work and Should I Use One?
As organizations increasingly adopt cloud services and applications, securing access to these services becomes crucial to protect sensitive data and maintain compliance. Cloud Access Security Brokers (CASBs) have emerged as a key component in providing comprehensive visibility and control over cloud services.
Dependency Management: A Guide and 3 Tips to Keep You Sane
Managing dependencies is not for the faint of heart. For a single project, you may be able to keep up with dependencies on your own. For software codebases with hundreds of modules, however, even the most seasoned developer will quickly descend into dependency hell. Don’t worry: dependency hell has happened to the best of us! There are some things you can do to keep yourself sane and improve application security.
Communication Service Providers Expect Strong Demand
Introducing new Zero Trust controls in ManageEngine PAM360
We are delighted to announce game changing features now offered as part of ManageEngine PAM360, our enterprise privileged access management (PAM) suite. With PAM360’s new additions to its Zero Trust offering, your organization’s privileged identities will be protected like never before. These updates will be available with the latest version of PAM360.