Deep Lateral Movement in OT Networks: When Is a Perimeter Not a Perimeter?
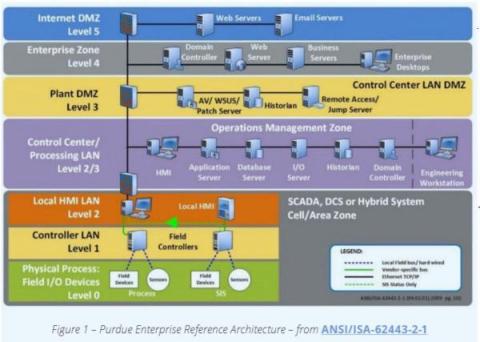
Forescout’s Vedere Labs latest research report is the first systematic study into deep lateral movement: how advanced adversaries can move laterally among devices at the controller level – also known as Purdue level 1 or L1 – of OT networks.