Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to Pick a Managed Security Service Provider: What You Need to Know
Finding the right security tools for your needs requires knowing who can offer them. Here is a guide on how to pick a managed security service provider.
68 Cloud Security Statistics to Be Aware of in 2023
We have adopted the cloud rather quickly. We’ve migrated our workloads in a haste at times, and we’ve developed cloud-native applications and adapted to a cloud-first business approach.
Win The AI Wars To Enhance Security And Decrease Cyber Risk
With all the overwrought hype with ChatGPT and AI…much of it earned…you could be forgiven for thinking that only the bad actors are going to be using these advanced technologies and the rest of us are at their mercy. But this is not an asymmetric battle where the bad actors use AI and the rest of us are struggling using our pencils and abacuses to catch up. It is the good side that invented and is accelerating AI. It is the good scientists that made ChatGPT and all of its competitors.
Recent Artificial Intelligence Hype is Used for Phishbait
Anticipation leads people to suspend their better judgment as a new campaign of credential theft exploits a person’s excitement about the newest AI systems not yet available to the general public. On Tuesday morning, April 11th, Veriti explained that several unknown actors are making false Facebook ads which advertise a free download of AIs like ChatGPT and Google Bard.
CTI Roundup: Threat Actors Use Self-Extracting (SFX) Archives for Backdoor Attacks
A new SFX exploit enables stealthy backdoor attacks, an ALPHV ransomware affiliate is targeting Veritas Backup Exec, and CTI tracks the emergence of Rorschach ransomware.
What is Code Signing? Benefits of DigiCert Code Signing Certificate
Whether you’re someone who creates computer software or just uses it, it’s essential to know about the code signing process. It is crucial to do so, as this is one of the methods that help you keep your computer safe and secure. Now, it might be possible that after reading the above content, you start wondering what code signing is and why it is important.
CISA Publishes Advisory on Improving Network Monitoring and Hardening
CISA released in late February a cybersecurity advisory on the key findings from a recent Cybersecurity and Infrastructure Security Agency (CISA) red team assessment to provide organizations recommendations for improving their cyber posture. According to the Agency, the necessary actions to harden their environments include monitoring network activity to spot abnormal behavior, conducting regular assessments and drills, and enforcing phishing-resistant MFA anywhere possible.
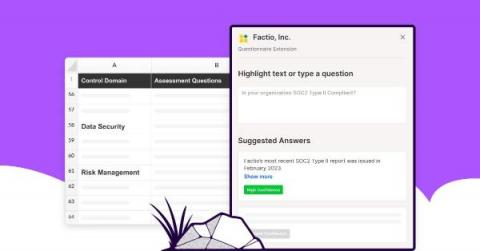
Introducing Questionnaire Automation
Following our recent acquisition of Trustpage, we are excited to announce Questionnaire Automation, a solution designed to help organizations in quickly responding to security questionnaires and effectively communicating security and compliance to customers and prospects. This solution utilizes the fastest and most accurate automation technology to provide security questionnaire responses.
What is Search Engine Phishing?
Search engine phishing, also known as SEO poisoning, is when cybercriminals use search engine optimization to appear as the top results on a search engine in an attempt to lead searchers to a spoofed website. The spoofed website is made to look like a legitimate site so that those who click on it proceed to log into their accounts like usual.