Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
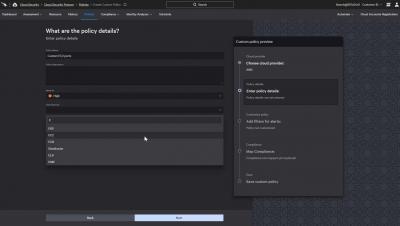
How to Create Custom Cloud Security Posture Policies
Falcon Horizon, CrowdStrike’s Cloud Security Posture Management solution, uses configuration and behavioral policies to monitor public cloud deployments, proactively identify issues and resolve potential security problems. However, customers are not limited to predefined policies. This article will review the different options for creating custom cloud security posture management policies in Falcon Horizon.
18 Best Cybersecurity Movies Worth the Watch
There are plenty of niche movie genres out there - road comedies, spaghetti westerns, Brenden Fraser films - all have their merits and their own special place in any true cinephile's heart. Today, we’re going to dive deep into the ridiculously specific micro-genre of cybersecurity movies.
Key Attributes You Need to Consider When Selecting a Cloud Security Platform
As more and more businesses move towards cloud-based operations and embrace digital transformation, security is increasingly becoming an important question. As an enterprise migrates to the cloud, its assets and data resources need to be migrated as well, and that might expose the sensitive information.
Runtime Protection: The Secret Weapon for Stopping Breaches in the Cloud
Mistakes are easy to make, but in the world of cloud computing, they aren’t always easy to find and remediate without help. Cloud misconfigurations are frequently cited as the most common causes of breaches in the cloud. According to a 2021 survey from VMware and the Cloud Security Alliance, one in six surveyed companies experienced a public cloud security breach or incident due to a cloud misconfiguration in the previous 12 months.
Deconstructing the Complexity of Managing Hybrid Cloud Security
There is a fine line between security and stability. So, how do you keep your IT assets running while maintaining a stringent security posture?
Charts - Sankey
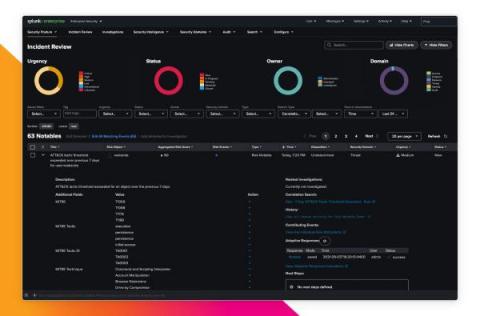
Splunk Releases Add-On for Google Workspace Security Monitoring
As the trend toward having a more distributed labor force working remotely part or full time persists, Splunk continues to see strong customer demand for more visibility into the security of the productivity and collaborative products their employees use. To assist with these requests, we’re excited to announce the release of Splunk Add-On for Google Workspace 2.0. This second major release includes important changes requested by our customers and valuable new functionality.
How Does Infrastructure as Code on AWS work?
Imagine having to manually provision and configure every device in a large corporation. Then visualize the upgrade process. How about patching? Then, picture ensuring conformity on every device. Next, add some enterprise-wide IT governance changes that must be implemented. The process would be daunting, to say the least, every time.
Catching A Wave, Standing Up on My Surfboard: How Cloud Threat Exchange Saves My SOC From Drowning (For Now)
We have built a Security Operations Center at Netskope in short order. Facing the vast expanse of the Security Operations ocean, I grabbed my board with my team and focused on doing a few things really well. We documented workflows, expanded our visibility, and tuned monitoring systems. We paddled out from shore, braving the shark-infested waters of the threat landscape.