Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
The Future of Cloud-delivered Security: Lookout Acquires CipherCloud
Today Lookout announced that we’ve acquired CipherCloud, a leading cloud-native security company that operates in the emerging Secure Access Service Edge (SASE) market. The combination will create the industry’s first company capable of providing an integrated endpoint-to-cloud security solution.
Navigating Transformation with Managed Cybersecurity Services
The coronavirus pandemic has added new layers to the threat landscape facing corporate security leaders in 2020 and going into 2021, as well. As businesses and workforces sought to adapt rapidly to remote working at scale, malicious groups and other threat actors began exploiting opportunities to target stressed people and systems with malware.
AIOps POC no longer have to be long and resource intensive
Quick Guide to the Difference Between a Public and a Private Cloud
Cloud security. Cloud architecture. Cloud storage. As you start scaling your business, you know “the cloud” is an important element of your IT capabilities. But, it can be a little confusing to understand the ins and outs of “the cloud” — especially when it comes to using cloud-based tools for your company to work remotely. Before we get into private vs public clouds, let’s quickly establish what we mean by cloud computing.
Two Major Industry Awards Confirm ChaosSearch's Growing Role in Enterprise Cybersecurity
What Does the HIPAA Safe Harbor Bill Mean for Your Practice?
Getting incentives for the best security practices is a win-win for all healthcare-related entities. For one, you are getting incentives, and secondly, you are making sure that you have a rock-solid defense in terms of security. Many organizations find that the rules and regulations that HIPAA entails are too extensive and overwhelming, however. What’s more, cybersecurity wasn’t a thing when HIPAA was introduced.
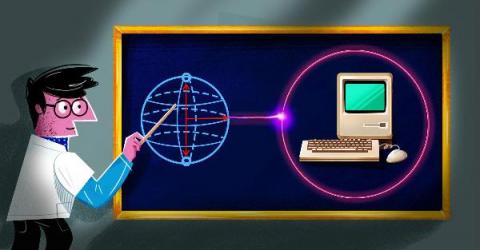
Five worthy reads: Understanding quantum computing and its impact on cybersecurity
Five worthy reads is a regular column on five noteworthy items we discovered while researching trending and timeless topics. In this week’s edition, let’s explore how quantum computing works and how it impacts cybersecurity.
Stories from the SOC - DNS recon + exfiltration
Our Managed Threat Detection and Response team responded to an Alarm indicating that suspicious reconnaissance activity was occurring internally from one of our customer's scanners. This activity was shortly followed by escalating activity involving brute force activity, remote code execution attempts, and exfiltration channel probing attempts all exploiting vulnerable DNS services on the domain controllers.
10 steps to cyber security for your business
In this article, you will understand what cyber security entails and the breakdown of NCSC’s 10 steps to cyber security that you must know. During our third party security validation exercises or customer communication, we have often come across customers without an answer to ‘what actually their IT and security products are protecting’. It is vital to be aware of what is important, what to protect and how to protect before shopping for security products.
Weekly Cyber Security News 12/03/2021
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. I’m not going to make any snappy and witty remark over this one as I feel the horror everyone must have felt seeing the photos and aftermath. We never hope to have to enact a DR plan, and after being there many years ago when I had to, believe me it is not fun even when prepared.