Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
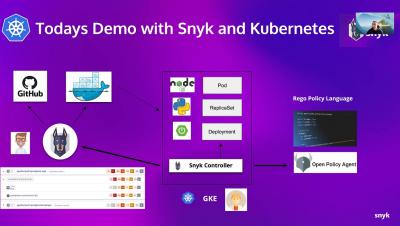
Automating Container Runtime Security Scanning with Snyk
A Kubernetes Controller for Styra DAS
We just open sourced our Kubernetes controller for the Styra Declarative Authorization Service (DAS). If you are interested in managing OPAs via Styra DAS via Kubernetes, read on.
Predict Cyber-attacks via digital twins
Several of the digital twin technologies out there have grown fast in only a few years. Picture establishing a virtual model of IT infrastructure where one can identify loopholes, create attack scenarios, and prevent catastrophic attacks before the system is officially put in place. Using digital twins, it's no longer a silly idea for organizations to follow. Let's get knowledge of Digital Twin technology and how it can help to assess the loopholes in your security posture.
What Does Sun Tzu Have to Do with XDR? More Than You Might Think!
Military general and philosopher Sun Tzu once led the largest armies in the world and authored The Art of War, still considered a masterpiece of tactical warfare and very relevant as we wage our battles against evolving cyberattacks. That’s because even though threat intelligence is a relatively new discipline in our cyber defense processes, it has actually been around for more than 2,500 years.
Snyk achieves AWS Security Competency status
We are very excited to announce that Snyk has achieved AWS Security Competency status, further validating our commitment to security excellence in partnering with AWS!
Java Security Tip: Sanitize user input
Data Protection Healthcare and Social Care | How to Store Information
The Data Protection Act is an important part of the cyber domain and legislation for anyone working in health and social care. It governs how to protect the information in health and social care. This blog post will explore the implications of the act on healthcare professionals, patients and other individuals who may have dealings with you as an organisation or individual providing care to others and the importance of protecting sensitive data in health and social care.
Monthly Cyber Vulnerability Bulletin - November 2021
Prepare for the next phase of work from anywhere security
Low-code is driving a tectonic shift in IT - can IT and security teams enable the business while also staying secure?
In recent years, we have witnessed a tectonic shift in the way organizations develop and maintain software. As part of this shift, IT operations are quickly getting decentralized.