Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
AWS Pentest Beginners Guide - Tools and Techniques
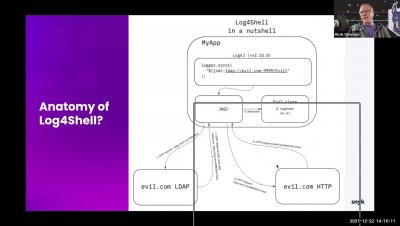
Snyk Log4Shell Stranger Danger Live Hack (APJ)
What is Digital Risk? Learn how to Manage it
Digital risks are a big issue for today’s society. Digital risks can be anything from stealing sensitive information to exposing your own personal information to the public. This is why an understanding of the digital risk management process helps businesses to identify and protect themselves.
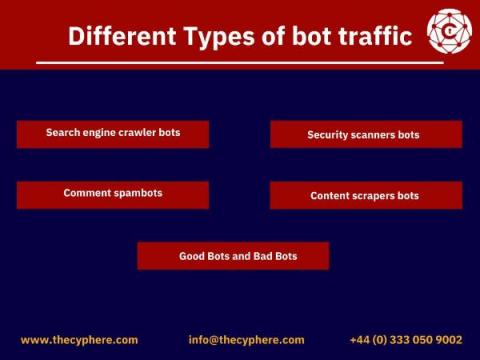
What are Traffic Bots? Methods to detect and stop Bot traffic!
Bot traffic is a type of traffic that is generated by automated programs, or bots. These bots can be used to generate fake traffic for testing purposes or to engage in malicious activities. Malicious bot traffic is a huge problem for many website owners, and bot detection can be difficult. There are various types of bot traffic that you need to watch out for. In this guide, we will discuss their different types and how to combat them!
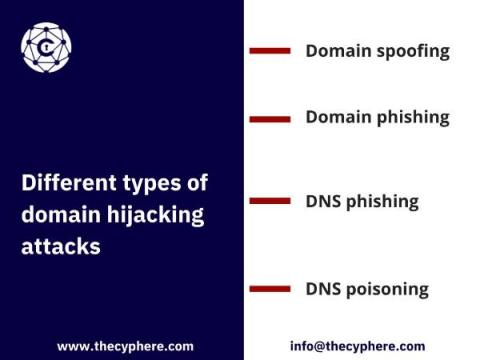
What is Domain Hijacking? Tips to Protect yourself
Domain hijacking is the act of domain name theft. It can happen to individuals or organisations and it’s increasing in frequency. The name may be hijacked by someone else who passes themselves off as you, tricks your domain registrar into transferring your domain to them, or hacks into your account (sometimes through phishing) and transfers it themselves.
Low-code Security Risks: 7 Sins and How to Overcome Every Single One
Low-code security vulnerabilities can be deadly - but not for you. Learn how to mitigate all the risks involved by downloading our free whitepaper “7 Deadly Sins of Low-Code Security and How to Avoid Them”. If you’ve followed our last two blog posts, you should already be familiar with the reasons why organizations that are undergoing digital transformation are turning to low-code development.
CVE-2021-44832: New Vulnerability Found in Apache Log4j
A new vulnerability was discovered in the Apache Log4j library. Tracked as CVE-2021-44832, this bug may allow arbitrary code execution in compromised systems when the attacker has permissions to modify the logging configuration file. CVE-2021-44832 has received a CVSS score of 6.6 out of 10, and it affects all versions of Log4j from 2.0-alpha7 to 2.17.0, excluding 2.3.2 and 2.12.4. This is the fourth Log4j vulnerability addressed by Apache in December 2021.
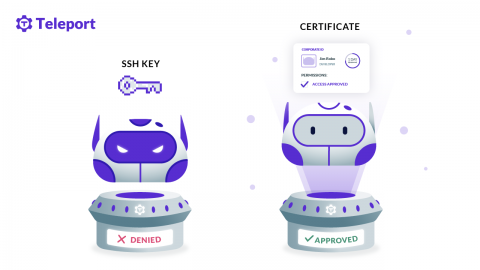
SSH Keys are Passwords Too
Use of misused or stolen credentials is the number one cause of data breaches. Using Password123 is worthy of a good laugh, but there are other passwords that are used everyday: SSH keys and other tokens used to access critical infrastructure. Teleport recently commissioned a survey of 1000 IT, DevOps and Security professionals and found that passwords are the number one way of managing access to infrastructure.
11 Steps to Secure SQL in 2022
Whether you’re running Microsoft’s SQL Server (soon to run on Linux) or the open source MySQL, you need to lockdown your databases to keep your data private and secure. These 11 steps will guide you through some of the basic principles of database security and how to implement them. Combined with a hardened web server configuration, a secure database server will keep an application from becoming an entry point into your network and keep your data from ending up dumped on the internet.
Will Zero Trust Shape the Future of Cloud Security?
Zero trust is everywhere, and it will change the way we undertake security. Just as zero trust concepts are shaping the data center and our networks, they will shape cloud environments, as well. Many of the challenges of cloud security arose because we moved workloads to the cloud with no clear idea of how to secure them. Zero trust provides exactly those ideas.