Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Anomaly Detection in Cybersecurity for Dummies
Elastic: Threat hunting with the Elastic Stack
Crossword Cybersecurity Plc acquires threat intelligence company, Threat Status Limited
Why SASE is your best bet to secure a remote workspace
The origins of Secure Access Service Edge (SASE) can be traced back to 2019, when legacy network security systems were extensively used in workspaces. Gartner defined SASE as the combined deployment of cloud-based cybersecurity functions, including Firewall as a Service, a cloud access security broker (CASB), a secure web gateway (SWG), Zero Trust network access (ZTNA), and software-defined WAN (SD-WAN).
Banish Shadow IT With Digital Footprint
It’s out there. In the deep, dark corners of your IT estate, it’s been hiding. Maybe it’s that “killer app” one of the department heads brought back from a trade show. Or maybe it’s that campaign microsite that marketing had a contractor develop for a “skunkworks” launch. Shadow IT is more than an asset management problem. It’s a security problem because you can’t secure what you can’t see.
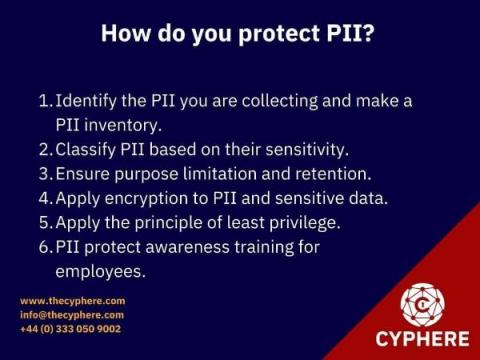
PII Protect Cybersecurity | How to Secure your Data
Over the last few years, the rise in data breaches involving personally identifiable information (PII) has resulted in the loss of millions of records.
Build a software bill of materials (SBOM) for open source supply chain security
More than ever, developers are building web applications on the foundations of open source software libraries. However, while those libraries make up the software bill of materials (SBOM) components inventory, not all developers and business stakeholders understand the significant impact on open source supply chain security that stems from including 3rd party libraries.
What Is a SIEM Use Case for Compliance and Security Risk
Due to rising trends and policy changes, organizations are opting for solutions that ensure a proactive measure of cybersecurity. Companies are being held to much higher standards on how they collect, store, and protect individuals’ data. So they are searching for solutions that are both cost-effective and accurate. SIEM software provides threat management along with a detailed and centralized view of enterprise security.