Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How to Create Custom Cloud Security Posture Policies
Falcon Horizon, CrowdStrike’s Cloud Security Posture Management solution, uses configuration and behavioral policies to monitor public cloud deployments, proactively identify issues and resolve potential security problems. However, customers are not limited to predefined policies. This article will review the different options for creating custom cloud security posture management policies in Falcon Horizon.
What is the Most Vulnerable Data My Company Holds?
Data security is on every priority list in 2022. With the frequency of breaches never higher, many businesses assess their situation and ask cybersecurity questions. With cybersecurity policy, everything boils down to risk. Ultimately, every decision-maker wants to know, “how likely are we to be attacked?” Many believe cybercriminals only target certain kinds of data. Sensitive information, high-value financial data, and medical records are all widely accepted to carry a high risk.
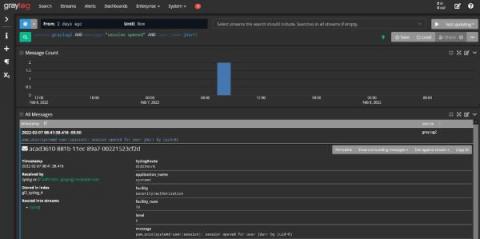
Using Log Management as a Security Analytics Platform
Offensive Security | Cybersecurity Sessions #6 with Jonathan Echavarria
18 Best Cybersecurity Movies Worth the Watch
There are plenty of niche movie genres out there - road comedies, spaghetti westerns, Brenden Fraser films - all have their merits and their own special place in any true cinephile's heart. Today, we’re going to dive deep into the ridiculously specific micro-genre of cybersecurity movies.
Getting the best out of your SIEM
1Password: The Heart of Cybersecurity Webinar Series: Pete Matheson
Outpost 24: Live Webinar: Why API security matters and how to get it right
WatchGuard: Elevating Your MSP Security Practice with a Unified Security Platform
How to Meet Third-party Risk Requirements of NIST 800-161
The National Institute of Standards and Technology (NIST) has produced several publications addressing the different components of information technology security within the NIST 800 computer security series. Compliance across this entire NIST 800 series is expected for all internal and external service providers of government entities - such as the DoD federal agencies.