Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Lookout Accelerates Zero Trust Journey for Ivanti Customers With SSE
To keep pace with the demands of a digital-first economy, organizations are accelerating cloud adoption and expanding work-from-anywhere initiatives. But as operations become more efficient, security teams struggle to keep pace. Existing solutions are not built to scale and can’t provide seamless access that safeguards data, which now reside in countless applications on premises and in the cloud.
Cybersecurity 101: Basic Terminology You Need to Know
(SBOM) Creation of your Software Bill of Materials
Missed last week's Defense & DIB Cybersecurity Summit? Watch the recording
Missed last week’s archTIS Defense & DIB Cybersecurity Summit with leading industry and defense experts? Watch the recording for their insights on the zero trust, CMMC 2 and the new threats the industry is facing and how to best combat them.
Top Security Information and Event Management Use Cases
Cyber security threats and measures mandated by regulations require an advanced security solution for organizations. Many reasons, such as false positives, difficulty in budget control, vulnerable protocols, and misconfigurations, can be confusing when choosing the right security solution. In order to get rid of all these concerns, security information and event management (SIEM) solutions come to the fore as solid and centralized security platforms.
How to counter smart home device breaches
This blog was written by an independent guest blogger. Businesses that allow employees to work from home are more likely to encounter a new security threat — compromised smart home devices. Smart technology connected to an employee’s home network, like smart thermostats, appliances, and wearables, can all fall victim to hackers. Workers that join their employer’s network remotely can unwittingly allow compromised devices to open the doors to hackers.
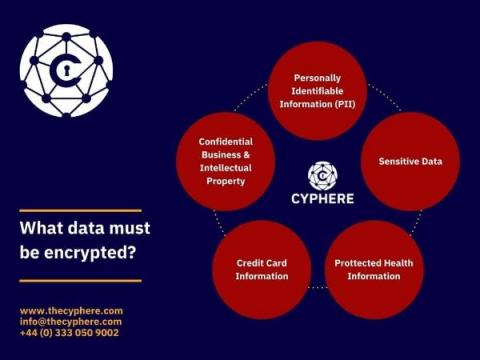
A Guide to GDPR Encryption
The current cyber threat landscape forces the secure handling of personal data, and data privacy laws such as the General Data Protection Regulation (GDPR) assist in enforcing essential security measures.
Elastic and Tines partner to detect security threats and reduce mean time to respond
Today, we’re happy to announce that Elastic and Tines are partnering to help our joint users detect security threats and reduce mean time to respond. Many of the world’s best security teams rely on the power of Elastic’s high-speed, cloud-scale detection, prevention, and response capabilities to investigate and contain potential security threats within their environments.