Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How to achieve FedRAMP Certification?
We previously covered the basics of FedRAMP by simply asking “What is FedRAMP?” This time, we’re going to talk about how you can get approved as a FedRAMP Cloud Service Provider (CSP). We’ll talk about some of the advantages of being FedRAMP authorized. We’ll also discuss FedRAMP compliance versus certification to understand the difference. Additionally, we will define terms you will need to know during your FedRAMP journey.
Introducing The Cybersecurity Defenders Podcast
Some of the most powerful moments in your career are when you are given the opportunity to create something new, to experiment, and give something back to the community that has been so supportive over the years.
Understanding DNS attacks: Identifying and patching vulnerabilities
The Domain Name System (DNS) translates domain names into IP addresses. Every device and website has an IP address that other devices, websites, and online services use to communicate with it. IP addresses are a string of numbers usually formatted as 000.000.000.000. However, we use domain names since people can’t easily remember these numbers.
How to Perform a Password Audit
In 2021, over two billion data records containing usernames and passwords were compromised, a 35% increase from 2020, according to ForgeRock’s Consumer Identity Breach Report. Weak passwords make it easy for cyberattackers to gain access to your network.
How to Stay Protected Against Student Loan Forgiveness Scammers
The Biden administration formally started the application for federal student loan forgiveness on Monday, October 17th, 2022. Recipients who qualify are eligible for the discharge of up to $10,000 of their loans for non-Pell Grant recipients and up to $20,000 for Federal Pell Grant recipients.
SOC Talent: How to Stay Competitive in the Hiring and Retention Game
The disparities in some key areas in our 2022 Devo SOC Performance ReportTM provide clear evidence that the issues facing organizations since the start of the global pandemic in early 2020 continue to affect SOC performance, especially in the areas of hiring and retaining SOC talent.
Webinar: Top Security Threats Worldwide: Q2 2022 - 20 October 2022
Data Driven Compliance
Security has been a top concern for years, and the reasons for this focus are increasingly clear. Government agencies are being asked by the President and governing agencies to make changes that will protect the integrity of their network and the safety of the nation.
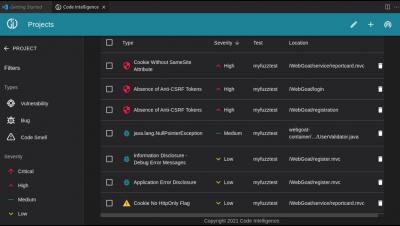
5 Stages of the Vulnerability Management Process
The threat landscape in IT is ever-evolving, with new risks arising practically daily. Trying to anticipate the next type of threat can feel a little like playing whack-a-mole. Instead, IT teams are focusing on vulnerability management: reducing the opportunities for hackers and other bad actors to find a weakness in cyber defenses. Vulnerability management is an iterative process that allows companies to proactively defend valuable assets, no matter how the threat landscape changes.