What Should You Expect from a Modern Network Threat Detection Platform?
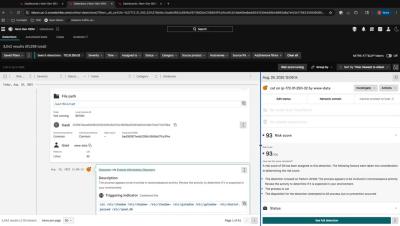
Many security teams struggle to see the full scope of threats because network, endpoint, and cloud data remain siloed. Without unified visibility, detecting hidden attacks or spotting lateral movement is tough. Gaps between tools lead to fragmented signals, low-fidelity alerts, and slower investigations. That fragmented view can let attackers linger longer—and SOC analysts bounce between multiple interfaces just to piece together a coherent incident narrative.