Phishing Attacks Are Rising: Automate Detection Before They Overwhelm Your SOC
Image Source: depositphotos.com
Phishing has become one of the most consistent and damaging entry points for attackers. Today’s campaigns aren’t the obvious scams we once knew. They look professional, mirror trusted brands, and often come packaged as full-service phishing kits with ready-made infrastructure.
For SOC leaders, this means one thing: the volume is climbing, and manual detection is no longer sustainable.
Why Manual Detection Can’t Keep Up
Most SOCs still depend on analysts to manually open suspicious emails, review attachments, and follow links step by step. At scale, that process creates bottlenecks. Each email burns valuable time, attention slips, and mistakes multiply.
Attackers know this. They hide behind QR codes, CAPTCHAs, and rewritten links, forcing analysts to dig deeper before the true threat is exposed. The result is alert fatigue, delayed response, and higher risk of compromise.
Leading SOCs Are Automating Phishing Detection
Forward-looking teams are shifting away from human-heavy workflows. Instead, they automate phishing analysis:
- Suspicious emails are ingested automatically
- Attachments and links are detonated in a controlled environment
- Hidden payloads, redirections, and credential theft pages are exposed without analyst clicks
- Indicators of compromise are extracted and exported for faster triage
This isn’t theory. It’s already working in production SOCs, helping them respond in minutes instead of hours.
A great example of this approach is ANY.RUN’s interactive sandbox, which automates the full phishing detection flow by simulating real user behavior. Unlike static tools, it actively engages with the threat, exposing hidden payloads, credential theft attempts, and attacker infrastructure. Analysts can also jump in and interact at any stage, adding their expertise without slowing the process. For SOC managers, this means faster investigations, more threats analyzed in the same timeframe, and smoother operations across the entire team.
How Automated Analysis Exposed a Real Phishing Attack in Less Than a Minute
Let’s take a look at a multi-stage phishing campaign that was fully uncovered inside the ANY.RUN sandbox in just 50 seconds. The analysis delivered complete visibility into the attack chain, detailed processes, TTPs, and all the relevant IOCs needed for a quick response.
View phishing attack exposed automatically

The initial email with a PDF attachment opened in the ANY.RUN sandbox
The investigation started once the suspicious email file was uploaded and Automated Interactivity was enabled. From there, the sandbox took over, simulating user actions without requiring any analyst clicks. It opened the message, launched the PDF attachment, and immediately detected a hidden QR code.
|
Help your team uncover phishing attacks in seconds, reduce analyst workload, and respond with confidence |
The embedded link was extracted, opened in a browser, and taken through the next stage.

The static discovering module in ANY.RUN lets you see the link hidden in the QR
To evade detection, the attackers had added a CAPTCHA roadblock, but the sandbox solved it automatically and continued.
The sandbox automatically solves CAPTCHA challenges
Within seconds, it reached the final destination; a convincing fake Microsoft login page designed to steal credentials. At that point, the system labeled the session as malicious, applied the “phish-url” tag, and captured every indicator along the way.
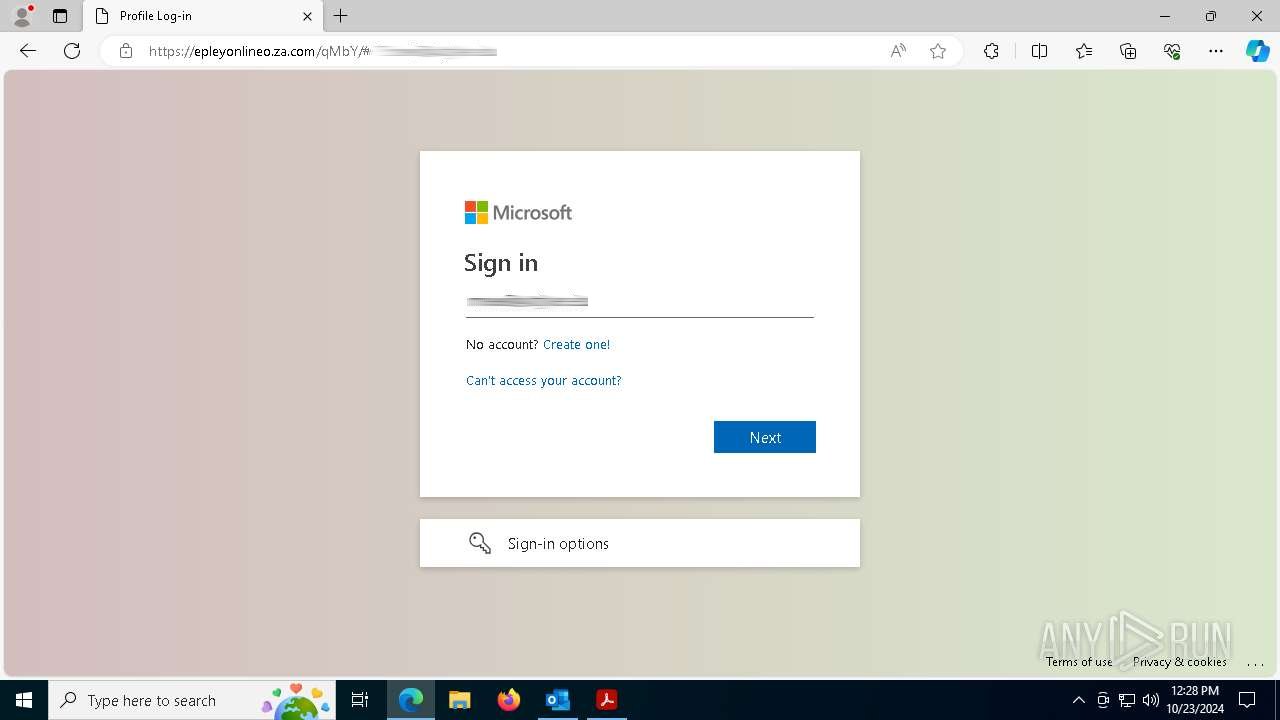
The final phishing page reached inside ANY.RUN sandbox
What would normally take an analyst several minutes of careful interaction was fully automated, producing a clear attack timeline, actionable IOCs, and a complete behavioral map that could be exported and shared immediately.

Well-structured report generated by ANY.RUN for convenient sharing
From Hours to Seconds: The Real Benefits of Automated Phishing Detection
Phishing campaigns are built to slip through defenses, hiding behind QR codes, CAPTCHAs, and convincing branding. With ANY.RUN’s interactive sandbox and automated detection, your SOC uncovers these threats in full, without burning analyst time on repetitive clicks.
- Clear verdicts in under a minute: Go from suspicious email to confirmed phishing case in as little as 50 seconds
- Less manual effort: The sandbox automatically opens files, follows redirects, solves CAPTCHAs, and exposes hidden payloads
- Reduced MTTR: Teams using ANY.RUN cut investigation times by up to 20 minutes per case, keeping incidents contained faster
- Relief for junior analysts: Routine phishing triage becomes manageable without constant senior oversight
- More impact for senior staff: Analysts can shift focus to proactive threat hunting, rule tuning, and strategic projects
- Higher throughput: SOCs report handling up to 3x more phishing cases within the same timeframe
- Smooth integration: Results flow directly into existing SIEM, SOAR, or XDR platforms via API and SDK
- Overall performance boost: Faster detection, fewer escalations, and greater visibility across phishing campaigns
For SOC leaders, the impact is clear: less time wasted, more threats analyzed, and stronger defenses without adding headcount.
Contact ANY.RUN to see how automated phishing detection can transform your team’s workflow and response speed.

