Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Something, Something, Hackathon: Rubrik Announces 6th Annual Hackathon Winners
Hackathons vary in sizes and shapes, but ours has typically been a 24-hour sprint, with teams submitting a five-minute video presenting their project. This year was our biggest hackathon yet, with almost 90 teams registering across a multitude of departments including Support, Sales, Product, Technical Writing, and, of course, Engineering! We crowdsource the first-round judging by asking anyone at Rubrik to participate in evaluating projects.
NC Protect for Microsoft Teams
How Achieving Compliance with PCI DSS Can Help Meet GDPR Mandates
Data security and privacy are today a prime focus for most organizations globally. While there have been several regulations and standards introduced to improve data security, the evolving landscape makes it challenging for organizations to stay compliant. For many organizations, GDPR and PCI DSS are the first topics that come to mind when privacy is concerned.
Scanning Amazon S3 Buckets with Nightfall Data Loss Prevention (DLP)
In this tutorial, we will walk through the end-to-end process of scanning your Amazon S3 buckets for sensitive data with Nightfall’s S3 Sensitive Data Scanner. By the end of this tutorial, you will have an exported spreadsheet report (CSV) of the sensitive data in your S3 buckets.
A Definitive List of Different Cloud Compliance Standards
Cloud security is not only good for consumers — but it’s also a requirement for businesses in many industries. Understanding compliance regulations (like GDPR) and security frameworks (like NIST) can help IT teams create strong, layered privacy and security controls and data loss prevention using a range of platforms and integrations. Here are the most common and comprehensive security standards that businesses need to know to be cloud compliant.
Do I need a VPN? How a virtual private network can protect you online
A virtual private network (VPN) is a useful tool that protects your online activity by creating a secure ‘tunnel’ that sits between your device and the site or service you’re trying to access.
NIST Standards and Guidelines for Enhancing Software Supply Chain Security Include Security Ratings
At SecurityScorecard, we believe that making the world a safer place means transforming how organizations view cybersecurity. For us, this means that companies must take a holistic approach, protecting systems not just from the inside, but also knowing what an organization’s vulnerabilities look like from the outside-in to see what the hackers are seeing.
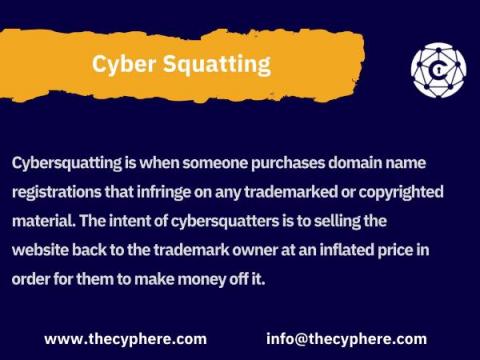
What Is Cybersquatting and how to prevent it?
Cybersquatting is a form of cyberspace domain name trademark infringement. In a nutshell, Cyber-squatters registered trademarks as domain names, typically selling the names back to the registered trademark owners at a profit.
Weekly Cyber Security News 12/11/2021
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. Way too many awesome articles to include caught my attention this week. These three made it though. When you become popular (OK, perhaps not totally correct) you do tend to attack the attention of those wanting to take a bite. This was perhaps then inevitable.