Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Speedcast and OneWeb Sign Partnership to Bring LEO Capabilities to the World's Largest Network
Your Current Endpoint Security May Be Leaving You with Blind Spots
Threat actors are continuously honing their skills to find new ways to penetrate networks, disrupt business-critical systems and steal confidential data. In the early days of the internet, adversaries used file-based malware to carry out attacks, and it was relatively easy to stop them with signature-based defenses. Modern threat actors have a much wider variety of tactics, techniques and procedures (TTPs) at their disposal.
Getting Started with Kubernetes Ingress
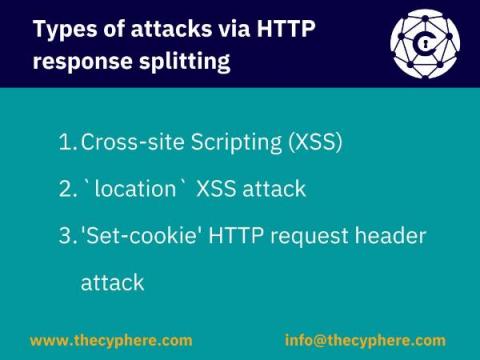
HTTP Response Splitting Attack
HTTP Response Splitting entails a kind of attack in which an attacker can fiddle with response headers that will be interpreted by the client. The attack is simple: an attacker passes malicious data to a vulnerable application, and the application includes the malicious data in the single HTTP response, thus leading a way to set arbitrary headers and embedding data according to the whims and wishes of the attacker.
Observability Pipelines & AIOps can make IT Smarter
4 Key Elements of A Good Cyber Hygiene
Top Recent Third-Party Breaches
The average company can’t do business without their third parties. Vendors, suppliers, partners, distributors, and contractors — third parties make it so much simpler to build, distribute and sell a product or service.