Ask SME Anything: What is Universal ZTNA?
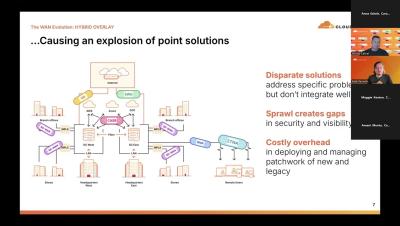
Most traditional access tools (VPNs, firewalls, and NACs) were never built for today’s hybrid world. If your legacy access tool is slowing you down, you need a different approach. In this episode of Ask SME Anything, Netskope expert Francisca Segovia explains how universal ZTNA redefines secure access for every user and device, anywhere. Life’s too short for slow connections. Reimagine your access architecture now with universal ZTNA from Netskope.