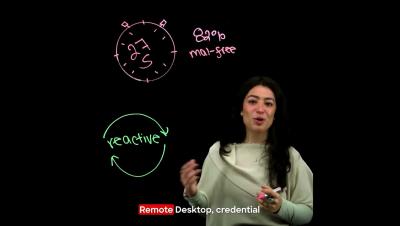
82% of Attacks Skip Malware Entirely
27 seconds. That’s how fast an adversary can move to your critical systems. In this clip, you’ll learn: How adversaries blend in using everyday admin tools Why traditional, reactive security models fall behind What makes modern intrusions so hard to detect Watch the full video to see how teams are shifting to proactive hunting.