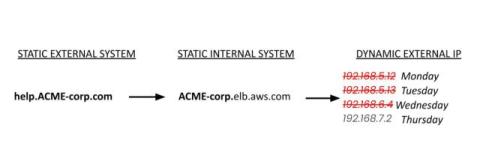
Claude Code reads a threat report, hunts for IOCs, and deploys detection rules #cybersecurity #ai
From threat intelligence article to deployed coverage. The AI agent extracts indicators, searches for compromise across tenants, confirms clean status, then creates and tests detection rules for ongoing protection within your LimaCharlie environment.