Open Source Supply Chain Security: Best Practices
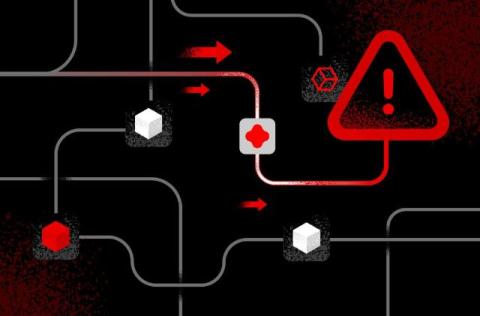
Open-source components are the building blocks of modern software, enabling your team to innovate and deliver features faster. This reliance, however, introduces a significant challenge: your application’s security is now tied to a vast and complex supply chain of code you didn’t write. The risks are escalating, with attackers targeting open-source libraries to launch widespread breaches.