Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
SIEM Implementation Strategies
A SIEM or Security Information and Event Management is only as good as its logs. People can think of logs as the fuel for the engine. Without logs (log management), the SIEM will never be useful. Selecting the right types of logs to ingest in your SIEM is a complex undertaking. On one hand, it is easy to say “Log it all!” but you will inevitably reach the glass ceiling of your SIEM, which will either be your licensing or you will cap the performance of the SIEM hardware.
Breaches Are Costing Companies Much More Than Money
On August 5, 2015, the British mobile phone retailer, Carphone Warehouse discovered a “sophisticated attack” on its systems, possibly compromising the personal information of 2.5 million customers and the encrypted credit card data of an additional 90,000 customers.
How Machine Learning Techniques Impact File Analysis
Applying machine learning (ML) and artificial intelligence (AI) techniques to analyze files within a content repository can raise the bar on operating efficiencies and produce smarter solutions that bring “structure” to unstructured data.
Why Zero Trust Is Not As Bad As It Sounds
"Zero Trust" refers to a network security strategy that calls for all users – internal and external – to be authenticated before gaining access to the network. Zero Trust means organizations never implicitly trust anyone with their sensitive data. Instead of using a blanket network perimeter, Zero Trust networks implement a series of micro-perimeters around data so only users with clearance to access certain data points can get to them.
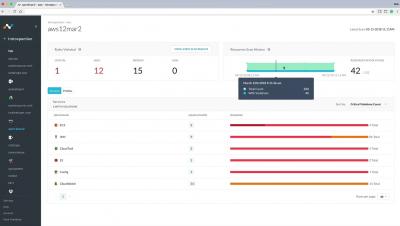
AlienVault® USM vs. OSSIM
Egnyte Connect for Google Hangouts Chat Lets Users Securely Share Content in Real-Time
New Integration Enables Seamless Collaboration and Increased Productivity in the Digital Workplace
Insider Enterprise Threats: User Activity Monitoring
Insider cyber security threats are much more prevalent than most of us realize.
4 reasons why cyber security deserves a larger chunk of your hospital organization's budget
In the medical community, the patient is paramount. There are countless methods employed to treat people and protect their health. But when it comes to their patients’ safety, most hospitals need a higher dosage of cyber security. Currently, health organizations are allocating less than half of what other industries budget for Information Security.