Protect Your Emails: Secure Sensitive Data with miniOrange DLP
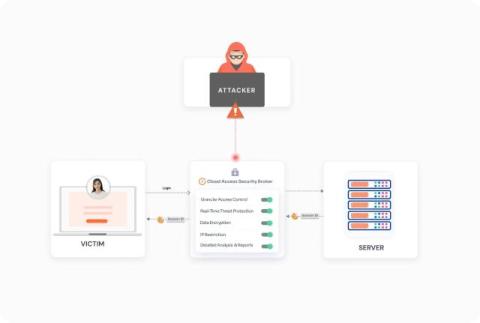
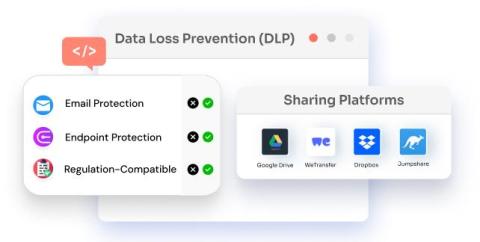
Did you know that over 90% of data leaks are caused by emails? With email data breaches increasing by 50% in the past year, businesses worldwide are at risk of financial losses, legal issues, and damaged reputations. Just one accidental email sent to the wrong recipient could result in a devastating data breach. In this video, we introduce miniOrange's Advanced Outbound Email Security Solution—a powerful tool designed to protect your organization's email communication. Here’s what you’ll learn: How to block outbound emails to prevent unauthorized messages.