Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
CISA Publishes Advisory on Improving Network Monitoring and Hardening
CISA released in late February a cybersecurity advisory on the key findings from a recent Cybersecurity and Infrastructure Security Agency (CISA) red team assessment to provide organizations recommendations for improving their cyber posture. According to the Agency, the necessary actions to harden their environments include monitoring network activity to spot abnormal behavior, conducting regular assessments and drills, and enforcing phishing-resistant MFA anywhere possible.
Introducing the Industry's First Unified, All-Software SASE Client with Integrated Netskope Endpoint SD-WAN and Intelligent SSE
There exists a drive in all of us that embraces innovation to make life easier. For IT leaders, it’s time for true innovation at the remote access edge.
AlgoSec - a single solution to secure application connectivity and accelerate policy changes
What is SD-WAN? | SD-WAN Explained #sdwan
Cloud WAF Pricing: All You Need to Know
Where Insider Threats Hide Out in a Segmented Network
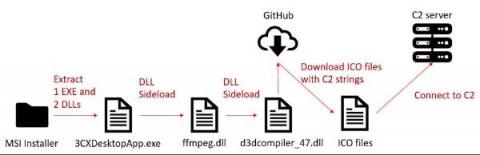
How to Detect and Mitigate the 3CXDesktopApp Supply Chain Attack
On March 29, researchers from two security companies identified an active campaign originating from a modified version of a legitimate, signed application: 3CXDesktopApp, a popular voice and video conferencing software. 3CXDesktopApp is developed by 3CX, a business communications software company. According to its website, 3CX has 600,000 client organizations and 12 million daily users.
Tame the CVE Beast using a Digital Twin
There are never enough hours in the day to do everything. I think we all have a to-do list that is at least twice as long as the time available to complete it. To cope, we prioritize what’s “on fire” or what has the most potential to immediately cause damage if it’s not taken care of. Often the things we “should” focus on fall to the wayside as they are outshined by what we must do immediately.
How SD-WAN and Public Cloud have changed the dynamics when it comes to modern connectivity and infrastructure requirements
Digital and cloud transformation has unlocked new business opportunities and operational efficiencies for organisations. But migration to the cloud also means our approach to deploying applications and services has radically changed, as enterprises move away from traditional data centres. Likewise, flexible working means users have also moved away from traditional offices and branches.