ModPipe POS Malware: New Hooking Targets Extract Card Data
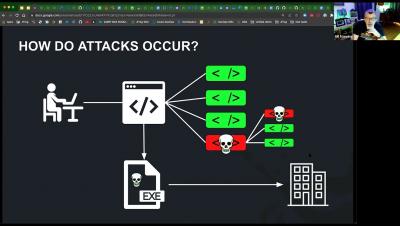
Kroll’s incident responders have seen threat actor groups becoming increasingly sophisticated and elusive in the tactics, techniques and procedures they employ to steal payment card data. One common method is to “scrape” the Track 1 or Track 2 data stored on the card’s magnetic stripe, which provides the cardholder account and personal information criminals need to make fraudulent “card-not-present” (CNP) transactions.