Cybersecurity Hygiene: Not a Dirty Little Secret for Long
In October 2018, FICO (a consumer credit scoring specialist) began scoring the cybersecurity of companies based upon a scan of internet facing vulnerabilities. FICO grades companies using the same scoring that is familiar with consumer credit. These metrics are then used to compare security risks against competitors. This announcement has the potential to be a sea change event in cybersecurity.
Serverless vs Cloud vs On-prem
Server architecture can differ in a lot of ways, but the three main categories would be on-prem, cloud and serverless. Some believe that cloud and serverless can be used interchangeably, which is not the case. To help clear up some confusion, this blog post will explain each of them and how it affects the security work.
Detectify security updates for 7 March
For continuous coverage, we push out major Detectify security updates every two weeks, keeping our tool up-to-date with new findings, features and improvements sourced from our security researchers and Crowdsource ethical hacker community. Due to confidentially agreements, we cannot publicize all security update releases here but they are immediately added to our scanner and available to all users. This post highlights a few things that we have improved in the last two weeks.
Kubernetes Security-Are your Container Doors Open?
Container adoption in IT industry is on a dramatic growth. The surge in container adoption is the driving force behind the eagerness to get on board with the most popular orchestration platform around, organizations are jumping on the Kubernetes bandwagon to orchestrate and gauge their container workloads.
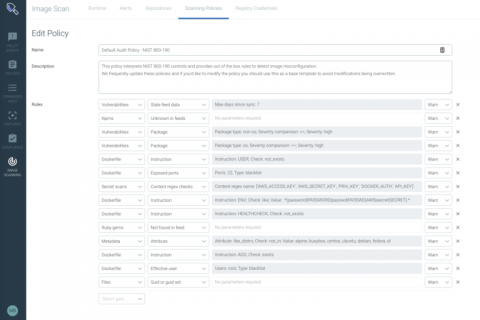
Better together with Sysdig and Anchore: Comprehensive container security across the software development lifecycle
In the new cloud-native world, ephemeral services like containers make security a challenging task. As enterprises start adopting containers in production, they suffer from a great deal of variance in the software, configuration, and other static artifacts that exist across their organization’s container image set.
Weekly Cyber Security News 08/03/2019
A selection of this week’s more interesting vulnerability disclosures and cyber security news. In the new GDPR age we are in, exploration of data at rest has been high on the agenda for many, and this item perked my interest – and some concern. Well worth a read.
Announcing the AlienVault Success Center!
We are very excited to announce that our new Success Center has just launched. It is our new “one stop shop” for help for AT&T Cybersecurity commercial USM Anywhere, USM Appliance and USM Central customers, OTX and OSSIM users, and InfoSec practitioners in need of help and support.
Internet of Termites
Termite is a tool used to connect together chains of machines on a network. You can run Termite on a surprising number of platforms including mobile devices, routers, servers and desktops. That means it can be used used to bounce a connection between multiple machines, to maintain a connection that otherwise wouldn’t be possible.
Integrating Detectify into your workflow
In the modern workplace, the work environment consists of many different teams, frameworks and tools to tackle complicated issues. It can be overwhelming to handle all the information transferred or continuously log into different tools to gather information. This is why Detectify offers 8 different software integrations, which sends web application vulnerability alerts from Detectify into your existing workflows or digital workplaces.