Create a Zero Trust strategy for your mobile workers
Lookout for Small Business: Secure Your Growing Business with Enterprise-grade Security
Java Crypto Catchup
In 2017, we started a blog series talking about how to securely implement a crypto-system in java. How to Get Started Using Java Cryptography Securely touches upon the basics of Java crypto, followed by posts around various crypto primitives Cryptographically Secure Pseudo-Random Number Generator (CSPRNG), Encryption/Decryption, and Message Digests. We also released a Java Crypto Module for easier dockerization of injectable modules exposing Crypto services via an API.
Managed Security Made Easy
Detectify Security Updates for November 16
Our Crowdsource ethical hacker community has been busy sending us security updates, including 0-day research. For Asset Monitoring, we now push out tests more frequently at record speed within 25 minutes from hacker to scanner. Due to confidentially agreements, we cannot publicize all security update releases here but they are immediately added to our scanner and available to all users. The following are some of the security vulnerabilities reported by Detectify Crowdsource ethical hackers.
Stories from the SOC - Multi-layered defense detects Windows Trojan
Malware infections are common and are often missed by antivirus software. Their impact to critical infrastructure and applications can be devastating to an organization's network, brand and customers if not remediated. With the everchanging nature of cyberattacks, organizations need a layered security strategy. They shouldn’t depend solely on a single layer of security to keep them protected.
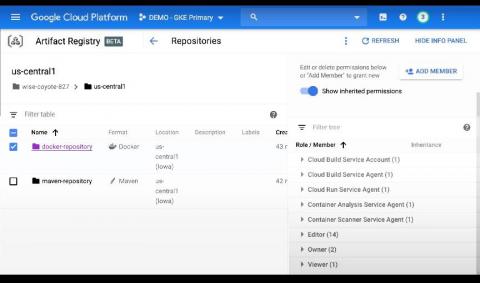
Sysdig extends image scanning to Google Cloud's Artifact Registry
In support of modern application development built on CI/CD, containers and open source, Google Cloud launched Artifact Registry (now generally available), a new artifact management solution. Sysdig helps DevOps teams using Artifact Registry confidently secure the build pipeline with comprehensive image scanning that identifies container vulnerabilities and misconfigurations to reduce risk.
7 Challenges that Stand in the Way of Your Compliance Efforts
Compliance is very important to any organization. Organizations have many standards to choose from including PCI, CIS, NIST and so on. Oftentimes, there are also multiple regulations that are applicable in any country. So, organizations need to commit some time and resources in order to apply security standards and achieve compliance. Even so, organizations encounter challenges when it comes to maintaining their compliance with security controls for their workflows, processes and policies.
SEC's Office of Compliance Inspection and Examinations Warns of a Sudden Increase in Credential Stuffing Hack
Recently, the Securities and Exchange Commission’s exam division issued a Risk Alert (the “Alert”) where it carried out several targeted cybersecurity investigations. The agency is now concerned with how there’s been an increase in a specific type of hack known as “credential stuffing.“ This cyberattack involves using stolen credentials to log into web-based systems and issue the unauthorized transfer of client funds.