Top 6 Hybrid Cloud Security Solutions: Key Features for 2024
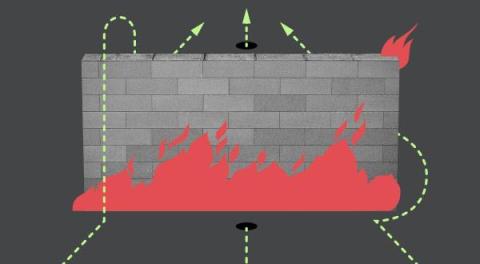
Hybrid cloud security uses a combination of on-premises equipment, private cloud deployments, and public cloud platforms to secure an organization’s data, apps, and assets. It’s vital to the success of any organization that uses hybrid cloud network infrastructure. The key factors that make hybrid cloud security different from other types of security solutions are flexibility and agility.