Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Seamless Collaboration in Life Sciences: A Key to Success
Biotech companies face an era of opportunities and challenges as data volumes explode and technology rapidly evolves. The pressure to enhance collaboration and efficiently manage data is immense. This article explores how innovative biotechs leverage platforms like Egnyte to transform their operations.
HTTP/2 Rapid Reset Attack Vulnerability
Cisco iOS XE Vulnerability: CVE-2023-20198
Cisco has released an advisory, acknowledging active exploitation of a previously unknown vulnerability, which is tracked as CVE-2023-20198, in the web UI feature of Cisco IOS XE Software when exposed to the internet or to untrusted networks. This vulnerability allows a remote, unauthenticated attacker to create an account on an affected system with privilege level 15 access, which is the highest level of access.
Elevating Enterprise API Security with Wallarm for MuleSoft Anypoint Platform
In an age characterized by digital transformation, APIs serve as the backbone of modern applications, enabling diverse systems to communicate and share data seamlessly. This widespread API adoption, however, exposes organizations to a considerable attack surface, inviting the attention of cyber adversaries searching for vulnerabilities to exploit.
What's XDR? Extended Detection & Response, Explained
Phishing Tests Start The Virtuous Cycle Of A Strong Security Culture
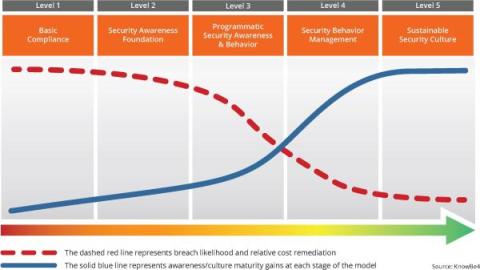
Phishing tests are the catalyst to achieve a sustainable security culture within your organization. They are actually the start of a virtuous cycle that helps you move up to the highest maturity level. The cycle initiates with Awareness. Phishing tests offer a real-time view into your employees' understanding of phishing threats. They expose your workforce to simulated phishing attempts, making the threat real to them. The immediate feedback from these tests highlights areas for improvement.
Summit Sabotage: Malicious Phishing Campaign Hits Female Political Leaders Using Social Engineering
A threat actor dubbed “Void Rabisu” used social engineering to target attendees of the Women Political Leaders (WPL) Summit that was held in Brussels from June 7 to 8, 2023, Trend Micro has found. “Since many current and future political leaders had attended this conference, it presented an interesting target for espionage campaigns and served as a possible avenue for threat actors to gain an initial foothold in political organizations,” Trend Micro says.
Cyber Insurers Notes Ransomware Claims Rose Significantly in the First Half of 2023
Cyber insurers are claiming that cybercriminals made ransomware attacks popular again in 2023 after a slight break in 2022. According to cyber insurer Coalition's 2023 Cyber Claims Report, claims frequency increased by 27% in the first half of this year compared to the second half of 2022. Additionally, cyber insurer Resilience Cyber Insurance Solutions mid-year report showed a similar trend with 16.2% of its total claims were related to ransomware attacks.
What is a CMDB?
There are countless tools and technologies available to help an organization stay on top of its IT assets, and a configuration management database (CMDB) is an extremely useful one. The database keeps track of relevant information regarding various hardware and software components and the relationships between them. It allows IT teams to have an organized view of configuration items (CIs) that can enable more streamlined processes when it comes to IT work.