Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Proactive Vulnerability Management is a No Brainer for Security, but...
In December 2022, the US Cybersecurity and Infrastructure Security Agency (CISA) identified exploits against vulnerable public-facing applications as the most common initial attack vector for cybercriminals, followed by attacks on external remote services such as VPNs. According to a study by CrowdStrike, exploit activity targeting cloud apps and assets grew 95% from 2021 to 2022, and instances of threat actors directly targeting cloud apps exploded by 288% during that period.
Polish Police Bust Dark Web Loan Extortion Ring: Fraudsters Face Up To 10 Years In Prison
Read also: Four people arrested over ChatGPT-linked ransomware attacks, a scammer charged for stealing $7.5M from two charities, and more.
Don't get hacked! Apply the right vulnerability metrics to Kubernetes scans
Application Security Challenges and Trends for the Year 2024
Every year, new technologies are released; with them, professionals are discovering new sets of application vulnerabilities. However, some threats and challenges are constant in the list, such as malware and app spoofing. However, all the threats are now more powerful with the advancement of tools. Further, it’s expected that the mobile app security challenges will be more rigid in 2024.
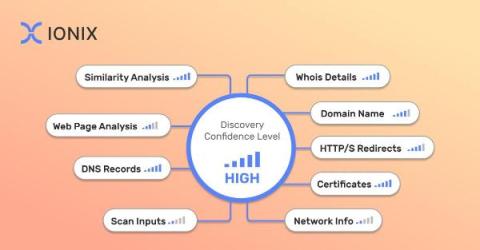
How to Implement Multi-Factor Asset Attribution in Attack Surface Discovery
As organizations navigate through the complexities of the digital era, the challenge of accurately identifying and managing their asset inventory has become a critical aspect of their security posture. This task, known as attack surface discovery and asset attribution, involves a delicate balance: identifying all assets that belong to the organization while ensuring that no extraneous ones are included.
Analyzing the Biggest Cybersecurity Exposure and Threat Events from 2023
Quantify Cyber Materiality When Navigating APRA's Regulations
Navigating the DoD's Proposed Rule: A Comprehensive Guide to CMMC Compliance Strategies
On December 26, 2023 the Department of Defense (DoD) unveiled the long-anticipated Proposed Rule for the Cybersecurity Maturity Model Certification (CMMC) Program, sending a clear message to defense contractors that CMMC is happening sooner than many thought, and that those taking a “wait and see” attitude can no longer wait to prepare.
Weekly Cyber Security News 04/01/2024
A selection of this week’s more interesting vulnerability disclosures and cyber security news. If there ever was a good example of what can happen if you don’t have a good password and no 2FA enabled, this is it.