Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Intrusion Prevention Systems explained: what is an IPS?
The goal of every cybersecurity strategy is to stop cyberthreats before they have a material impact. This has resulted in many organizations seeking to be more proactive in their response to potential threats by employing solutions to detect and prevent specific types of cyberattacks by monitoring for the earliest indicators of attacks found within network traffic.
Redscan Q&A: Cyber Security Innovation with Paul Sutton
We are better together: AT&T USM Anywhere and Digital Defense Frontline
Detecting the threat after collecting the right data is the first step. From there, the impact of the threat really matters; otherwise, security teams may be chasing after too many issues.
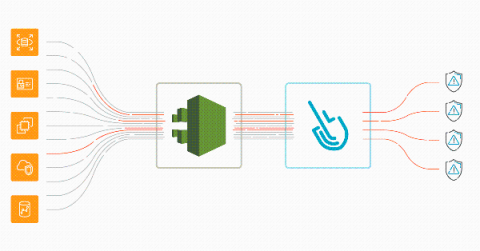
AWS threat detection using CloudTrail and Sysdig Secure
Implementing AWS threat detection with Sysdig Secure takes just a few minutes. Discover how to improve the security of your cloud infrastructure using AWS CloudTrail and Sysdig Cloud Connector. With the rise of microservices and DevOps practices, a new level of dangerous actors threatens the cloud environment that governs all of your infrastructure. A malicious or inattentive cloud API request could have a sizable impact on availability, performance, and last but not least, billing.
Practical security engineering: Stateful detection
Detection engineering at Elastic is both a set of reliable principles — or methodologies — and a collection of effective tools. In this series, we’ll share some of the foundational concepts that we’ve discovered over time to deliver resilient detection logic. In this blog post, we will share a concept we call stateful detection and explain why it's important for detection.
Protecting Fleet Data from Security Threats
Big data is revolutionizing fleet management — specifically in the form of telematics. From engine diagnostics that track fuel efficiency and mileage to sensors that detect aggressive driving behavior and interior vehicle activity, this information is so valuable that we’re quickly approaching the point where connected technology will come standard in every vehicle. Telematics is an operational goldmine.
Best Practices for Scoring Your Environment's Security Measures
For most practical uses today, a combination of hardening and vulnerability detection is required to secure even the most basic digital environment. In each area it is important to see the progress you’re making in these competencies so that you can improve and build on the work you and your team have done over time. But with so many assets in your digital environment, how do you score the effectiveness of these security measures?
OSINT - Using Threat Intelligence to Secure Your Organisation
In my first article on Cyber Security Threat Intelligence Analysts, (CTI analysts) we covered what a CTI analyst is and discussed how they can bridge the gaps between IT, Security, and the Business. We discussed how this is beneficial to the maturity of the business, but what exactly did we mean by this? In the second article of our CTI analyst series, we’ll cover the unique benefits a CTI analyst brings to an organization by enhancing.
Threat Modeling in Times of Crisis
With most of the country sheltering in place and so many people working remotely, work-life balance is taking on a new meaning and cloud infrastructure is taking a beating. The dramatic increase in daily activity and network use is creating both a visibility challenge and an operating model shift for already lean security teams.