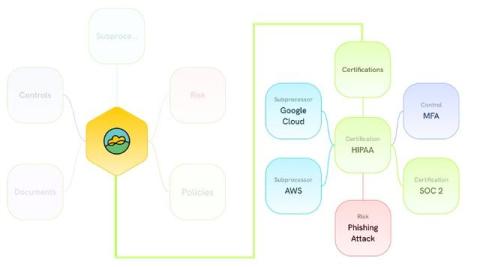
Integrating control graphs for holistic risk management
Enterprises around the globe are transitioning to integrated frameworks that encompass multiple risk dimensions, ensuring that risk identification, evaluation, and mitigation are conducted in a holistic manner. One of the emerging methods in this domain is the integration of control graphs into risk management frameworks.