Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Beneath the AI iceberg: The forces reshaping work and security
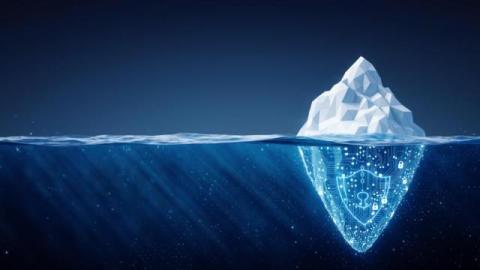
In conversations about AI, there’s a tendency to treat the future like a horizon we’re walking toward, always somewhere ahead, always a question of when. But if we look closely, the forces reshaping work, identity, and security beneath the surface are far more consequential than most people realize. More importantly, that reshaping is already happening.
6 ways Persona's Graph helps you fight sophisticated and scaling fraud
For fraud fighters, link analysis tools like Persona’s Graph are becoming essential for stopping account sharing, deepfakes, identity mules, and other forms of sophisticated or scaling fraud attacks. Since we launched Graph in early 2023, we’ve spent countless hours gathering feedback from customers, investigating the latest fraud vectors, and testing new technology. Graph is a better product as a result, and we want to share six improvements that are helping fraud fighters today.
SIEM Automation to Improve Threat Detection and Incident Response
Security professionals often compare their jobs to a game of “Whack-a-Mole,” the arcade game where players try to hit little plastic moles on the head. The moles pop up in a randomly generated way, making it difficult to predict which one will show its little head next.
Is Prevention the New Pillar of Cybersecurity?
For a long time, cybersecurity has been built around two basic actions: detecting and responding to cyber threats. However, automated attacks, advanced malware, and AI-driven threats show that reacting is no longer enough. Today’s attacks move fast, and in most cases, the damage is already done by the time they are detected. This is nothing new: organizations need to get ahead of risk and protect their systems before incidents occur.
How to choose the best risk management software for your organization
Fast-paced changes in technologies, regulations, and growth expectations can quickly shift your risk environment. Without a structured approach to managing these risks, even the most innovative organizations can face costly disruptions, security incidents, and compliance missteps.
Identity & Beyond: 2026 Incident Response Predictions
In 2026, incident response (IR) will continue its shift away from traditional malware-centric investigations toward identity-driven intrusions, abuse of trusted cloud services, and low-signal, high-impact activity that blends seamlessly into normal business operations. Rather than relying on technical exploits, threat actors are prioritizing legitimate access, persistence, and operational efficiency, enabling them to evade users, security controls, and automated detection.
Beyond Testing: API Security as the Foundational Intelligence for an 'industry leader'-Level Security Strategy
In today's security landscape, it's easy to get lost in a sea of acronyms. But one layer has become the undisputed foundation for modern application security: API security. Why? Because APIs are no longer just part of the application, they are the application. They are the connective tissue for microservices, third-party data, and the explosive new 'Agentic AI Action Layer' powered by protocols like MCP (Model Context Protocol). Securing the application is securing the APIs.
A Day Without ICS: The Overlooked ICS Risks That Could Bring Operations to a Halt
Have you ever watched AMC’s The Walking Dead? Before the walkers, before the chaos, there is a quieter moment that often goes unnoticed. The power is out. Roads are empty. Hospitals are running on borrowed time. The world has not fallen apart yet, but it is no longer working. That is what a day without ICS and OT would look like. Industrial control systems (ICS) and operational technology (OT) are the systems that run the physical world.
See the Attack Before It Lands: What the ARMO-Rapid7 Partnership Unlocks
The ARMO-Rapid7 partnership connects broad attack surface coverage with deep cloud and Kubernetes runtime security and visibility. By correlating exposures with real workload behavior, organizations can identify meaningful risk earlier, focus remediation where it matters most, and respond to active threats with precision, improving security outcomes while operating more efficiently in cloud-native environments.