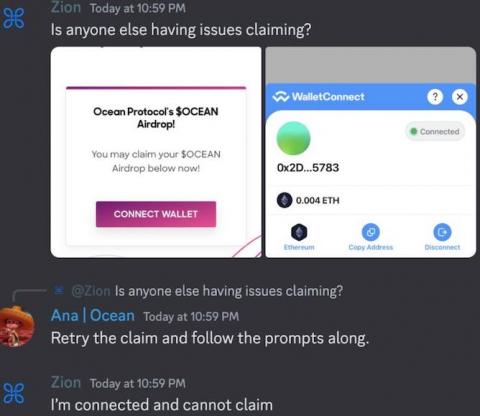
The Bookmark Trap: How Discord Admins Fell Prey to Social Engineering
Brian Krebs wrote: "A number of Discord communities focused on cryptocurrency have been hacked this past month after their administrators were tricked into running malicious Javascript code disguised as a Web browser bookmark. "According to interviews with victims, several of the attacks began with an interview request from someone posing as a reporter for a crypto-focused news outlet online.