Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cybersecurity in the Entertainment Industry: Risks and Solutions
The Vermont Dept of Financial Regulation Gets Breached, Exposing 42K Residents
The Vermont Department of Financial Regulation is an organization that oversees the financial sector within the state. The department is split into four divisions: Securities, Banking, Captive Insurance, and Insurance. Any businesses involved in these companies must answer to this department, and many Vermont residents have supplied the department with information to help it carry out its everyday role.
Beware of Clickbait PDF Phishing Attacks Lurking in Search Results
We previously reported independently on PDF-based phishing attacks skyrocketing and the rise of SEO attacks. A recent research study found that the combination of both is quite common. Most worryingly, PDF-based SEO attacks are poorly detected by common defense mechanisms such as blocklists, ad blockers or even crowdsourced antivirus services VirusTotal. PDF-based attacks can be anything from a website embedded in a PDF file to an email.
4 pillars of automated least privilege access
For decades the principle of least privilege has been a fundamental component of cybersecurity. The principle of least privilege revolves around granting users the minimum level of access necessary to perform their tasks, minimizing the risk of unauthorized access and data breaches.
Healthcare System Growth Requires Trusted Access Management
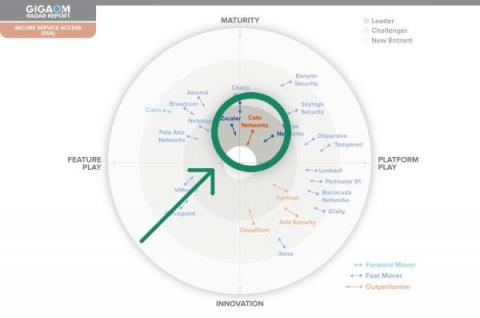
Cato SASE Cloud: A Two-Time Leader and Outperformer in GigaOm's Radar Report for Secure Service Access
In the ever-evolving world of cybersecurity, enterprises are constantly seeking the most effective solutions to secure their networks and data. GigaOm’s Radar Report for Secure Service Access, GigaOm’s term for SASE, provides a comprehensive look at the industry, and for the second consecutive year, names Cato Networks a “Leader” and “Outperformer.” The recognition points to Cato’s continuous commitment to innovation and improvement.
What is a Whaling Attack and How to Prevent It
Five worthy reads: Strengthening cybersecurity-exploring vital legal provisions
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week we are exploring vital legal provisions to strengthen cybersecurity. The digital environment has developed into a fertile ground for cybercrime in today’s connected society. Governments all across the world have realized the need for extensive legislative protections for people, organizations, and national security due to the increase in cyberattacks.