Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Role of API Inventory in SBOM and Cyber Security
Creating a Software Bill of Materials (SBOM) is crucial to software supply chain security management. It helps fortify your software supply chain and reduces the likeliness of your software being exploited. But did you know there's a way to enhance your software's security further? Well, that's when API inventory comes into the picture. Including API inventory in your SBOM can make your software solution more resilient to cyberattacks.
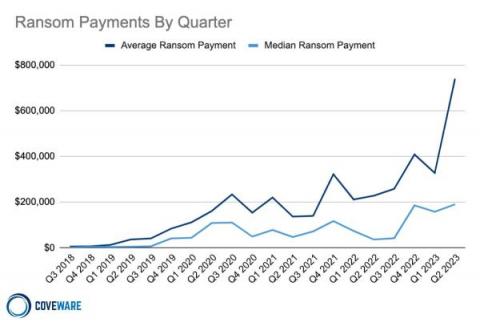
Ransomware's Paradox: Why Falling Monetization Rates Are Accompanied by Soaring Ransom Payments - A Must-Read Analysis.
Grab a cup of coffee, and let's talk about something that's been making waves in the cybersecurity world: ransomware. You've probably heard about the alarming rise in ransom payments, but did you know that ransom monetization rates have actually fallen to a record low? It's a complex and evolving landscape, and we're here to break down the recent very interesting Coveware report for you.
Social Media Platforms Become Half of all Phishing Attack Targets
Social platforms are the current favorite target of cybercriminals, displacing financial institutions, providing cybercriminals with credentials to be used as launch points for further phishing campaigns. Most cyber attacks we read about seem to involve an organization that was attacked because it was perceived to have a lot of money that could be parted with via ransomware, extortion, digital fraud, etc.
Online Scams Targeting Individuals Double in a Single Quarter as Global Risk Rises
New analysis of the second quarter of this year makes it clear that individuals and organizations alike are at an increasing risk of web- and email-based scams.
Ransomware Attacks Surge as Generative AI Becomes a Commodity Tool in the Threat Actor's Arsenal
According to a new report, cybercriminals are making full use of AI to create more convincing phishing emails, generating malware, and more to increase the chances of ransomware attack success. I remember when the news of ChatGPT hit social media – it was everywhere. And, quickly, there were incredible amounts of content providing insight into how to make use of the AI tool to make money.
Cybercriminals May Already Have Hacked Your LinkedIn Account
New reports show many LinkedIn users have reported complaints about accounts being taken over by bad actors. In a statement from Cyberint researcher Coral Tayar, "Some have even been pressured into paying a ransom to regain control or faced with the permanent deletion of their accounts," The reported complaints are on other social media forum platforms such as Reddit, Microsoft, and X with several users expressing frustration due to the lack of response from their support team.
New Vulnerability in tree-kit: Prototype Pollution - CVE-2023-38894
2023 KuppingerCole Leadership Compass Report: Managed Detection & Response Services
KuppingerCole has named Kroll as an Overall Leader in its latest analysis of the Managed Detection & Response services market. The KuppingerCole Leadership Compass provides an overview of the market for managed detection and response (MDR) services that manage a collection of cybersecurity technologies to provide advanced cyber threat detection and response capabilities, including Security Operations Center as a Service (SOCaaS) offerings.
BSidesLV: The big event before the biggest security event in Las Vegas
BSides Las Vegas 2023 united security experts and devs. Highlights include PasswordsCon, medical device security, MFA challenges, and CISA's role in cybersecurity.