Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
One Plugin, Four IDEs: Building a Consistent Security Experience Across Developer Tools
If you regularly work across IDEs, you’ve probably noticed how security tools often behave inconsistently. One plugin might work well in VS Code but feel clunky in PyCharm or Visual Studio. We set out to change that. The Veracode Scan plugin delivers a consistent, reliable experience across VS Code, JetBrains IDEs, Eclipse, and Visual Studio — helping developers focus on writing secure code, not troubleshooting plugins.
MURKY PANDA: A Trusted-Relationship Threat in the Cloud
Since 2023, CrowdStrike Services and CrowdStrike Counter Adversary Operations have investigated multiple intrusions conducted by MURKY PANDA, a sophisticated adversary leveraging advanced tradecraft to compromise high-profile targets. MURKY PANDA, active since at least 2023, is a cloud-conscious adversary with a broad targeting scope; the adversary’s operations have particularly focused on government, technology, academia, legal, and professional services entities in North America.
CVE-2025-54253: Zero-Day Vulnerability in Adobe Experience Manager Forms
A critical zero-day (CVSS 10.0) in Adobe Experience Manager (AEM) Forms JEE 6.5.23.0 and earlier allows authentication bypass and remote code execution (RCE). AppTrana delivers immediate Day 0 protection with: Virtual patching before vendor fixes Continuous monitoring of exploit attempts 24×7 security team ensuring zero downtime With a public PoC already available, the risk is high. Apply the patch ASAP or protect instantly with AppTrana WAAP.
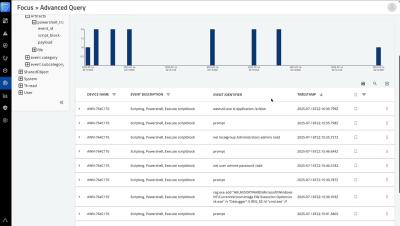
How to use Advanced Queries in Aurora Endpoint Defense
This demo uses the Advanced Query capability in Aurora Endpoint Defense to investigate an alert and learn that it was a part of a larger attack.
Can You Kill an API Token in Real Time? Here's Why It Matters #apikeys #api #incidentresponse
What happens if an API token or key is compromised? The ability to instantly revoke or block tokens during an incident is critical to stopping attackers. In this clip, Wallarm and Oracle experts discuss real-world challenges in detecting and disabling malicious tokens—and why mature incident response and tooling are essential for API security.
Mastering ESXi CLI: Full Tutorial on esxcli Commands for VMware vSphere
Learn how to unlock the full power of the ESXi command-line interface in this in-depth walkthrough. From enabling SSH and navigating esxcli namespaces to managing storage, networking, VMs and software packages — this video is packed with practical examples for real-world administration of VMware vSphere environments. Topics covered include: Enabling SSH and accessing the ESXi shell Exploring the structure and syntax of esxcli.
Fidelis Deception: Enterprise Insider Threat Solution
Insider threats drain organizational budgets by $17.4 million annually on average, with over 80% of companies experiencing at least one insider-related incident in the past year. Existing insider threat solutions deliver inadequate protection because of excessive false positives, sluggish threat detection, and weak intelligence gathering capabilities.
Warning: Social Engineering is a Growing Threat to the Industrial Sector
Social engineering attacks are a growing threat to operational technology (OT) environments, Industrial Cyber reports. Cyberattacks against these environments can be particularly damaging since they have the potential to cause physical disruptions.
Phishing Attacks Target Brokerage Accounts to Manipulate Stock Prices
Professional phishing groups are targeting customers of brokerage firms in order to manipulate stock prices, KrebsOnSecurity reports. The attackers use a technique called “ramp and dump” to profit from the scheme. “With ramp and dump, the scammers do not need to rely on ginning up interest in the targeted stock on social media,” Krebs explains.
New Homoglyph Phishing Campaign Impersonates Booking.com
Attackers are using a Japanese Unicode character to replace forward slashes in phishing URLs, BleepingComputer reports. The attacks impersonate Booking.com with phony emails that inform users of a new login to their account. “The attack, first spotted by security researcher JAMESWT, abuses the Japanese hiragana character “ん” (Unicode U+3093), which closely resembles the Latin letter sequence '/n' or '/~', at a quick glance in some fonts,” BleepingComputer explains.