Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
The Unmeasurable is Unmanageable: Why Cyber Resilience Takes Center Stage for Businesses
The World Economic Forum (WEF) recently published an article on cyber resilience that resonates with conversations we have daily at Arctic Wolf. Their central argument — that organizations need to move beyond basic prevention toward comprehensive, measurable resilience — reflects what we’re hearing from business leaders across industries.
What's Behind The Rise of Spear Phishing Attacks on IT Leaders?
Phishing has been a mainstay of cybercrime for decades – and for good reason. Threat actors continually evolve their phishing tactics, techniques, and procedures (TTPs), adapting the method with new tools and technologies to ensure it remains highly effective. IT leaders have become especially attractive targets: their privileged access amplifies the impact of a successful compromise.
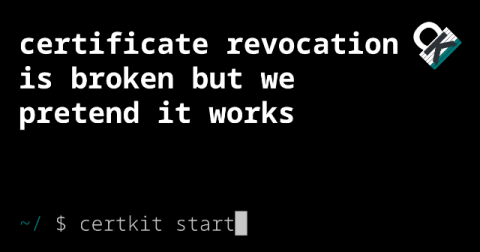
Certificate revocation is broken but we pretend it works
Last week, someone commented on my post about 47-day certificates: This perfectly captures our collective delusion that SSL certificate revocation works. You click a button, the certificate stops working. And why wouldn’t we believe that? Every CA has a big “Revoke Certificate” button right there in the dashboard. It must do something, right? Here’s the dirty truth: most revoked certificates keep working.
Seven Bibliography Mistakes SparkDoc Catches, Plus How to Keep Them Out of Your Drafts
Good writing can wobble at the finish line when the references go wrong. Reviewers notice. Teachers notice. Readers who care about sources notice first of all. Bibliography mistakes do not only weaken credibility, they slow down the whole process because every small error leads to another round of checking. This guide looks at the errors that appear again and again, plus how an AI-aware workflow reduces them without turning the page into a sales pitch. The goal is a clean, verifiable bibliography that supports the argument rather than distracts from it.
Behind the Laughs: The Security Measures Keeping Meme Coins Safe
In the fast-moving crypto world, meme coins have evolved from internet jokes into serious digital assets with multi-million-dollar market caps and thriving communities. But their playful origins sometimes make people question how secure they really are. Projects like Shiba Inu, Dogecoin, PEPE, and countless others rely on advanced blockchain protocols and community-driven safeguards to maintain a high level of stability and trust. Understanding these protective layers is essential for anyone interested in joining the wave of digital finance.
How Responsible AI Governance Strengthens Cybersecurity Defenses
Here's something that should keep you up at night: cybercrime might cost the global economy $10.5 trillion every year by 2025. That's not a typo. Traditional security measures? They're already struggling to keep pace. Attackers have figured out how to weaponize artificial intelligence, launching sophisticated campaigns that waltz right past conventional defenses like they're invisible.
Forescout: Forescout eyeSentry: Continuous Threat and Exposure Management for the Modern Enterprise
Cyber risk isn't standing still. It's evolving rapidly across increasingly complex, distributed environments. Traditional security tools and periodic assessments can't keep up, often leaving organizations with critical blind spots and compliance gaps. Enter Forescout eyeSentry: a unified, cloud-native platform purpose-built for Continuous Threat and Exposure Management (CTEM). Join us for an exclusive webinar where we'll unpack the details behind eyeSentry and show you why it's a critical component to implementing an effective continuous threat and exposure management program.
Snyk: Vulnerabilities on the Radar
Join us each month for an insightful webinar hosted by Vandana Verma Sehgal and Wesley Bentura, where we bring you the latest in the ever-evolving world of cybersecurity.
Reach Security Recognized as a CRN® 2025 Stellar Startup!
Reach Security announces that CRN , a brand of The Channel Company, has included Reach Security on its 2025 Stellar Startups list in the Security category. This prestigious list highlights fast-rising technology vendors that are driving innovation and fostering growth in the IT channel with groundbreaking products.
What Can an Outsourced Cyber Security Company Do for Me?
Outsourcing cyber security is becoming increasingly common for UK organisations of all sizes. With cyber threats growing every year, many businesses simply do not have the in-house resources, staff, or specialist skills to stay protected. Recent UK government data shows that 48% of small businesses experienced a cyber breach in the last 12 months, and over 70% of companies say they lack the internal expertise needed to manage cyber risks effectively.