Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Weekly Cyber Security News 11/10/2019
A selection of this week’s more interesting vulnerability disclosures and cyber security news. Amazing, if not scary selection of news items this week. However, I’m going to pick out three curious and on the face of it ones that would otherwise fly past without interest. The first, and its a subject that really interests me: How do the scammers succeed at social engineering so frequently? Perhaps we can learn a little bit more from this one.
What is Defense in Depth?
Defense in depth is a cyber security strategy that uses a series of layered, redundant defensive measures to protect sensitive data, personally identifiable information (PII) and information technology assets. If one security control fails, the next security layer thwarts the potential cyber attack. This multi-layered approach reduces the cyber threat of a particular vulnerability exploit being successful, improving the security of the system as a whole and greatly reducing cybersecurity risk.
Webinar: The Problem with Firewalls and Kubernetes, and How to Solve it
Vulnerability Remediation Tracking
Vulnerability remediation tracking is one of the important components of cyber security practices. In this blog post, we gathered all the necessary information you must have in regards to this topic.
Love your enemies before you destroy them
The cutting edge of cybersecurity is moving away from a reactive defense. Instead of analysts waiting for a threat to happen, they are proactively searching out attackers in their environment. Attackers are dynamic. They are always changing and improving their capabilities, which means that defenders need to lean in and adapt even faster to keep up. Proactive defense is about predicting, understanding, and preventing as many moves as possible that an attacker could make against you.
Teleport Overview Webinar
How to: On-premise Server Update
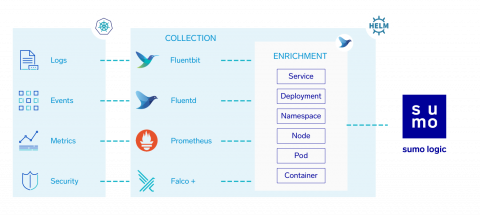
Kubernetes DevSecOps with Sumo Logic
What is CVE? Common Vulnerabilities and Exposures Explained
Common Vulnerabilities and Exposures (CVE) is a list of publicly disclosed information security vulnerabilities and exposures. CVE was launched in 1999 by the MITRE corporation to identify and categorize vulnerabilities in software and firmware. CVE provides a free dictionary for organizations to improve their cyber security. MITRE is a nonprofit that operates federally funded research and development centers in the United States.
What's new in OTX
Alien Labs and the Open Threat Exchange (OTX) development team have been hard at work, continuing our development of the OTX platform. As some of you may have noticed, we’ve added some exciting new features and capabilities this last year to improve understanding within the OTX community of evolving and emerging threats.