Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Using the Graph Chart
Data Protection Act | 8 Principles under GDPR
Security Risk Management for Insolvency, Restructuring and Bankruptcy Firms
Using the Voronoi - Data Search and Activeboards
Sophisticated Tardigrade malware launches attacks on vaccine manufacturing infrastructure
Security researchers are warning biomanufacturing facilities around the world that they are being targeted by a sophisticated new strain of malware, known as Tardigrade. The warning comes from the non-profit Bioeconomy Information Sharing and Analysis Center (BIO-ISAC) which revealed that at least two large facilities working on manufacturing bio-drugs and vaccines have been hit by the same malware this year, in what appear to be targeted attacks.
How to Make Slack HIPAA Compliant in 2022
As digital transformation continues post-COVID more organizations, including those covered by HIPAA, will seek out SaaS solutions that make collaboration easier. Fortunately more and more applications like Slack are enabling HIPAA compliant use. In early 2019 as Slack filed for its IPO, the company also updated its security page to provide details on its qualifications as a HIPAA compliant messaging app.
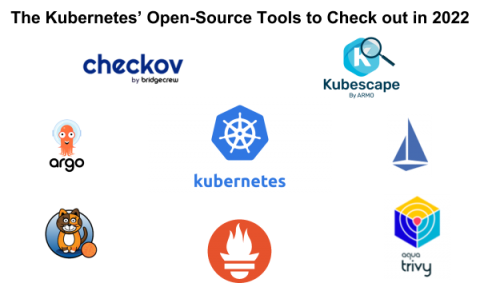
The Kubernetes' Open-Source Tools to Check out in 2022
In 2014, Kubernetes surfaced from work at Google and quickly became the de facto standard for container management and orchestration. Despite its silicon valley origins, it became one of the most impactful open-source projects in the history of computing. Today, the Cloud Native Computing Foundation (CNCF) maintains Kubernetes with many private companies and independent open-source developers.
Interview with Bill Kunneke, Chief Technology Officer at Leasecake
For our latest specialist interview in our series speaking to technology leaders from around the world, we’ve welcomed Bill Kunneke, Chief Technology Officer at Leasecake. Bill has over twenty years of experience as an IT professional and a proven technical leader who delivers large and often transformative IT projects while communicating complex technical solutions to key stakeholders and executing strategic IT functions.
The Oculus (Meta) Quest Scam
Oculus (also now known as Meta) Quest is a virtual reality headset and game craze created by Facebook, and it is the ultimate tech must-have for the holidays in 2021. My 11-year-old son is obsessed with it and during the past few months it has been impossible to get due to a recall and the wait for the new Quest 2 to be released.
Guide to Performing a Data Risk Assessment
Most companies know how to engage in a security risk assessment. However, the first step in the security assessment process should be engaging in a data risk assessment. While the two sound similar, they provide different insights. This guide to performing a data risk assessment explains what it is, why it’s important, and how to engage in one.