Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
A Weaponized npm Package '@core-pas/cyb-core' Proclaimed Pentesting Related
Two packages of well-known origin were found exfiltrating Windows SAM and SYSTEM files, apparently as part of internal security research rather than a targeted dependency confusion attack. On June 6th, 2022, the Mend research team used Supply Chain Defender to detect and flag two malicious packages from the same author that contained identical code. We alerted npm and the packages were removed within three hours of publication.
How Rubrik Supports the NIST Cybersecurity Framework Profile for Ransomware Risk Management
Rubrik was built on a foundation of Zero Trust architecture. The National Institute of Standards and Technology (NIST) is a United States federal agency that works with organizations of all sizes to help them implement cybersecurity best practices.
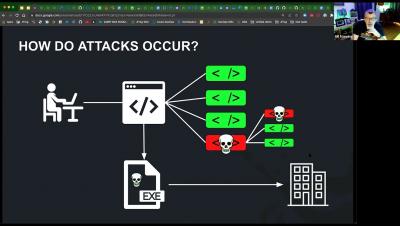
Stranger Danger: Your JavaScript Attack Surface Just Got Bigger
What Are Web Cookies? The Privacy and Security Risks of Internet Cookies
This article has nothing to do with chocolate chips or sprinkles. Sorry about that. Instead, we're talking about computer cookies and how too many web cookies can be bad for your online health. While cookies are enormously helpful and necessary for an easy-going web experience, they are not all good, and many pose some genuine privacy concerns. But what is a cookie, how does one work, and how do they (sometimes) infringe on your digital rights?
Tigera: Microsoft and Tigera: Hands-on AKS workshop: Configuration Security and Compliance
Tigera: Prevent a potential DDoS Attack with Application-Layer Security Controls
Rubrik: Introduction to Rubrik: Zero Trust Data Protection
Introducing NC Protect's New CUI Designator Labelling Capability for US Defense Requirements
Protecting Controlled Unclassified Information (CUI) is a top priority for companies that have government and defense contracts, especially with the changes being rolled out in CMMC 2.0. We’re pleased at announce a new NC Protect watermarking feature to support CUI Designator labelling capability to assist US Defense and the Defense Industrial Base (DIB) with meeting the new CUI document handling and tagging requirements. The feature will be globally available during the July 2022 timeframe.
Protect your Business with Enterprise Mobile Security in 2022
If you are not taking enterprise mobile security seriously, look at these stats: According to the State of Enterprise Mobile Security 2022 Report, 75% of the analyzed phishing sites targeted mobile devices. The same report stated that 30% of the total zero-day vulnerabilities discovered in 2021 targeted mobile devices. Security week states that mobile phishing attacks have increased at a consistent rate of 85% since 2011.