Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Microsoft Discovers Security Flaws In Pre-installed Android Apps
Four high-severity vulnerabilities have been exposed to the framework used by pre-installed Android system apps with millions of downloads. Fixed by Israeli developer MCE Systems, this issue could allow an attacker to launch remote and local attacks or be used as a vector to exploit extensive system privileges to obtain sensitive information. Here’s what Microsoft 365 Defender Research Team had to say about it.
What is the NIST Framework? An Introduction and a Look at Its Five Core Functions
The National Institute of Standards and Technology is an agency within the U.S. Department of Justice. It was founded in 1901 to support science and technological development. For decades, it has provided guidance on computer security. In 2014, in cooperation with public and private sector experts, the NIST released its cybersecurity framework. The framework combines best practices and industry standards to help organizations deal with cybersecurity risks.
What is the Difference Between Cyber Resilience and Cybersecurity?
Cyber attacks and data breaches are top of mind for businesses around the world as attacks on vulnerable networks persist. It is now more important than ever to ensure cybersecurity and resilience. But how do these two practices differ? This blog highlights the differences between cybersecurity and cyber resilience and how to secure your business for optimal cyber protection.
How Risk Intelligence Impacts Cyber Readiness
While your security staff tends to work the same business hours as everyone else, it often feels like threat actors never take a day off. Because an attack can and will come from any direction at any time, an organization’s cyber readiness is paramount. Your cyber readiness is the level at which you’re able to identify and respond to an attack.
Improving Clinical Operations Efficiency through Network Analytics
In any organization and in largely any industry, most network analytics are driven by IT. Healthcare providers are no exception. The insights extracted via network analytics offer serious opportunities for operational improvements and added value across departments. There are also significant ancillary benefits from a more cyber-aware and “plugged in” organizational posture — including improved information sharing, collaboration, and security.
Democratizing Data Using a DataFabric & How it Benefits IT Enterprises
Stories from the SOC - Detecting internal reconnaissance
Internal Reconnaissance, step one of the Cyber Kill Chain, is the process of collecting internal information about a target network to identify vulnerabilities that can potentially be exploited. Threat actors use the information gained from this activity to decide the most effective way to compromise the target network. Vulnerable services can be exploited by threat actors and potentially lead to a network breach. A network breach puts the company in the hands of cybercriminals.
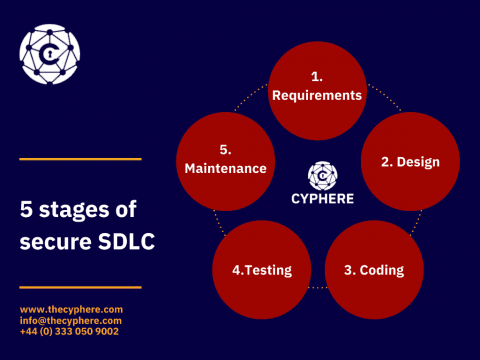
Secure software development lifecycle (SDLC) Best Practices
With all the remote works, online businesses, and digital lifestyle, applications (software) have become an integral part of our lives. In contrast, the growing rate of data breaches and cyber-attacks exploiting minor glitches in application functionality has diverted attention to application security which is still underrated in the era of phenomenal technological advancement.
What is Cache Poisoning?
Network security is of the utmost importance when it comes to protecting servers. An organization's servers contains a lot of sensitive data (e.g., clients’ personal data) that can greatly harm your business in the blink of an eye if compromised. One of the most common yet often undetectable ways the security of your servers can be compromised is cache poisoning. It is crucial to be aware of what cache poisoning is, how it works, why it is so dangerous, and how you can prevent becoming a victim.
Emotet: Still Abusing Microsoft Office Macros
In April 2022, Netskope Threat Labs analyzed an Emotet campaign that was using LNK files instead of Microsoft Office documents, likely as a response to the protections launched by Microsoft in 2022 to mitigate attacks via Excel 4.0 (XLM) and VBA macros.