Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Ingesting CrowdStrike Falcon Platform Data into Falcon Long Term Repository
Threat hunters and security teams need more data about the IT environment to add context to their investigations. To add that additional information to your Falcon environment, Falcon Data Replicator (FDR) gives you a way to pull raw event data from the CrowdStrike Falcon® platform. Now, customers can ingest, transform and analyze the data as part of their standard process.
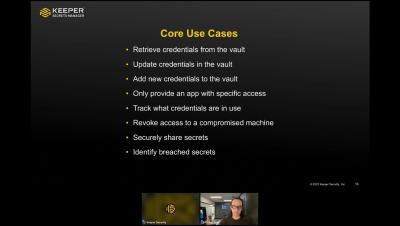
Keeper Secrets Manager: Remove Hard-Coded Credentials Forever
Privileged credentials are some of the highest-value targets for cybercriminals – is your organization still hard-coding credentials and putting itself at risk? Keeper Secrets Manager is a fully managed cloud-based, zero-knowledge platform for securing infrastructure secrets such as API keys, database passwords, access keys, certificates and any type of confidential data. Watch this recorded webinar to learn how to secure your environment and eliminate secrets sprawl with Keeper Secrets Manager – finally remove hard-coded credentials forever!
What is a Gap Assessment?
The NIST Cybersecurity Framework (CSF) provides a list of best practices organizations can follow to maintain a secure environment. At first glance, the list can seem quite complex! When Sedara works with a client to improve their security posture, we do in-depth information gathering. The questions asked might include things like: How do you keep your computer systems updated? How often are they updated? How do you manage adding access for new hires, and ending access for terminations? Do you provide your staff training so they are up-to-date on security threats?
Riscosity State of the digital supply chain Mike Hamilton and Barak Engel
In this video we talk with two security leaders, very well known, from the Bay Area - Mike Hamilton and Barak Engel. A variety of topics, including software supply chain, data governance and APIs amongst many are discussed.
Data Privacy in Healthcare: An Introduction to Protecting Patient Data
Healthcare organizations routinely handle large amounts of sensitive data, making data privacy in healthcare a top priority. Protecting patient data is not just about compliance—it’s crucial for maintaining patient confidentiality and safety. Unauthorized access can be severely detrimental, leading to breaches that compromise medical records and erode trust. Over the years, the digital revolution in healthcare has greatly elevated patient care standards.
jazzer.js
Coverage-guided, in-process fuzzing for the Node.js
jazzer
Coverage-guided, in-process fuzzing for the JVM
Tigera: Securing the container build pipeline with Image Assurance
The core principles in DevOps process especially for security have been to shift left and incorporate vulnerability management early in the build cycle. One way to successfully reduce the chances of introducing vulnerabilities in a container environment is to integrate an image scanner which can help identify and prioritize risks in container images. Calico's Image Assurance solution is built around these principles.
Tigera: AWS Dev Days - Hands-on workshop: Implementing Container Security on EKS
Attend this in-depth, hands-on EKS focused workshop with an AWS expert and Calico expert to learn how to detect and manage vulnerabilities and mitigate risks from security threats during the build and run time. The 90-minute interactive lab comes with your own provisioned Calico Cloud environment and is designed to help.
Tigera: Microsoft Azure: Hands-on AKS workshop: Implementing Zero-Trust Security for Containers
In this AKS-focused workshop, you will work with a Calico and Microsoft Azure expert to learn how to implement Zero-Trust security for workloads running on AKS. This 90-minute hands-on lab comes with your own Calico Cloud environment.