Critical Mobile Security Capabilities Everyone Needs
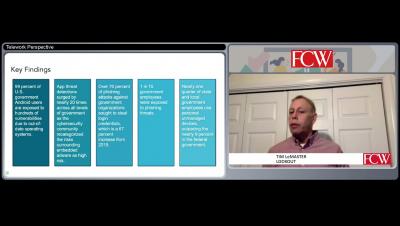
One thing that 2020 taught us is that you can do anything with a mobile device. My smartphone and tablet have become my go-to for shopping, banking, watching TV and video chatting with family and friends. I’m also getting a lot of work done on them. Basically it has become the center of both my personal and professional lives. Here’s the dilemma a lot of organizations are facing: while away from the office, your workers are using their mobile devices to stay productive.