Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
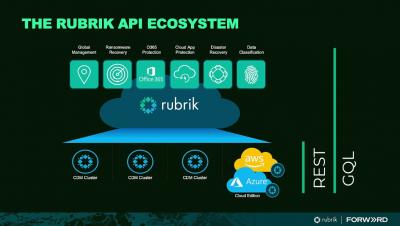
Rubrik and GraphQL - Episode 1 - REST vs GraphQL
Cross Account Replication of AWS RDS with Rubrik Security Cloud
The Relational Database Service (RDS) service offered by AWS is one of the most popular databases today. A lot of critical, confidential data resides inside of RDS. Hence it becomes imperative to protect this data from various threats and ensure that the data is secure. Our approach to protecting the data inside RDS is based on two aspects: Rubrik already supports a modern approach to safeguarding RDS data from an operational perspective and also maintains a clean, secure copy in a different region.
Cloud Threats Memo: The Growing Risk of Misconfigured Internet-facing Servers
Misconfigured internet-facing servers are a growing risk for organizations and one of the preferred weapons for ransomware gangs to break into their victims’ networks.
Lookout Talks Online Mobile Security for Students
Data Resilience for Microsoft Azure SQL Against Ransomware and Credential Compromise
In the event of a cyber attack, how confident are you that your Azure SQL data is safe and recoverable? As a commitment to cyber-proofing the cloud, we’re pleased to introduce new security enhancements to our previously-announced Azure SQL protection. Now, businesses and government agencies can further minimize the risk of data loss in Azure SQL databases and Managed Instances.
Stay Vigilant: How Cloud Interconnectivity Is Amplifying the Effects of Phishing
It seems like every week another household brand announces that they’ve been the victim of a data breach. Recently, cloud communications company Twilio announced that its internal systems were breached after attackers obtained employee credentials using an SMS phishing attack. Around the same time, Cloudflare, a content delivery network and DDoS mitigation company, reported that its employees were also targeted but their systems were not compromised.
Blackhat 2022 recap - Trends and highlights
Blackhat 2022, on its 25th anniversary, took place this week in Las Vegas. The most important event for the infosec community and the best place for security vendors to showcase all their innovations and products in this ever-growing ecosystem. This year, attendees come from 111 different countries. In 2020, Black Hat added the word Cloud to the existing track about Platform Security.
How to Comply with HECVAT in 2022
The Higher Education Community Vendor Assessment Toolkit (HECVAT) helps higher education mitigate the impact of security risks of vendor relationships offering cloud-based services. With supply chain attacks on the rise, and vendor risks ranking in the top three initial attack vectors for data breaches, HECVAT compliance is becoming a mandatory requirement for partnering with higher education institutions.
5 Misconceptions about Mobile Application Security Testing
All app development companies are aware of the importance of mobile application security testing. Despite this, the app stores are full of potentially vulnerable apps. One of the reasons for this is the myths surrounding the mobile application security testing concept - how it might be complicated or expensive to get security. However, this blog will dispel these myths and present a true picture of mobile application security testing.