From Neural Networks to Threat Networks: How AI Development is Reinventing Security Intelligence
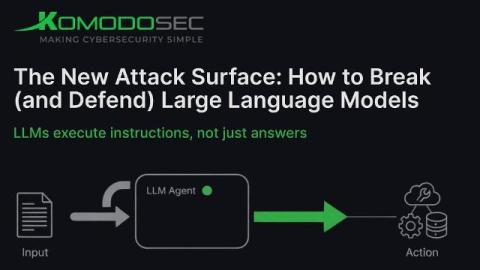
In the digital age, the landscape of cybersecurity is evolving faster than ever. Threat actors are becoming increasingly sophisticated, while traditional security measures struggle to keep pace. Enter Artificial Intelligence (AI)-an innovation that is transforming security intelligence by converting neural networks, traditionally used for pattern recognition, into threat networks capable of predicting, detecting, and mitigating cyberattacks in real time.