Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
CrowdStrike Adds New Strategic Partners to Groundbreaking CrowdXDR Alliance
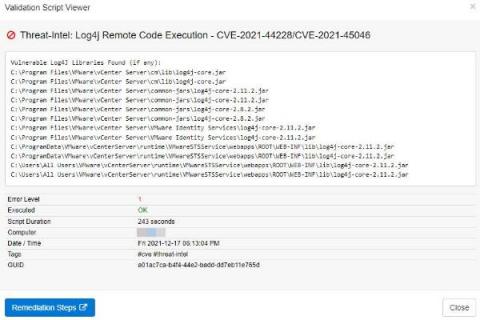
Discovering vulnerable Log4J libraries on your network with EventSentry
Just when the Microsoft Exchange exploit CVE-2021-26855 thought it would win the “Exploit of the year” award, it got unseated by the – still evolving – Log4J exploit just weeks before the end of the year! Had somebody asked Sysadmins in November what Log4J was then I suspect that the majority would have had no idea. It seems that the biggest challenge the Log4J exploit poses for Sysadmins is simply the fact that nobody knows all the places where Log4J is being used.
SecurityScorecard CISO Mike Wilkes talks about 2022 Cybersecurity Predictions
The Top 9 Cybersecurity Predictions for 2022
Cyberattacks are constantly evolving as criminals discover new ways to crack strong networks or automate attacks to target vulnerable systems. Nowadays, it seems as if cyberattacks are everywhere you look. In 2021, we faced many new attack vectors as the shift to remote work challenged traditional work operations, and we are likely to see those continue well into 2022.
Threat hunting: Process, Methodologies, Tools and Tips
In cyber security, threat hunting is the act of proactively searching and monitoring networks, systems, endpoints, datasets etc. to identify any malicious behaviours or patterns that are not detected by existing security tools.
Live Hacking: Find Vulnerabilities in Your Apps Before Hackers Do
CrowdStrike
The CrowdStrike Falcon OverWatch SEARCH Threat Hunting Methodology
CrowdXDR Alliance Expands to Help Security Teams Identify and Hunt Threats Faster
CrowdStrike is proud to announce that Armis, Cloudflare and ThreatWarrior have joined the open CrowdXDR Alliance. The addition of these industry leaders enhances XDR with telemetry from cloud, network and Internet of Things (IoT) solutions.This best-of-platform approach to XDR will help solve real-world productivity challenges that security teams face by empowering them to identify and hunt threats at accelerated speed and scale.